Campaigns
Applications
Access Request/Identity Lifecycle Management
Audit Trail
Ticketing/People
Security
Added the Ability to Create Hierarchical Campaigns
Added the Ability to Send Additional Escalation Emails to Upper-Level Management
Added the Ability to Include BCC in Emails
Added Fields to the Fuzzy Match Page
AWS Cloud Storage Connector – New Connector
On-Prem Jira Connector – New
AWS IAM Identity Center Connector – New
AWS Cloud DB Connector – New
Ultipro (UKG) Connector – Updated
AD Connector – Show Nested Entitlements by Default
Workday Connector – Improved Failure Messaging
WebAPI Connector – Added Support for Oauth 2.0
Added a Configuration to Be Able to Request Access for Any Application, Regardless of Group Assignment
Improved Request Access UI
Added the Ability to Request All Application Types
Added an Audit Trail for Administration Configurations
Added Ticketing for ManageEngine ServiceDesk
Added the Option to Use the Two-Step Checkout Model in Service Now Request
Upgraded to Latest MySQL Version 8.0.34
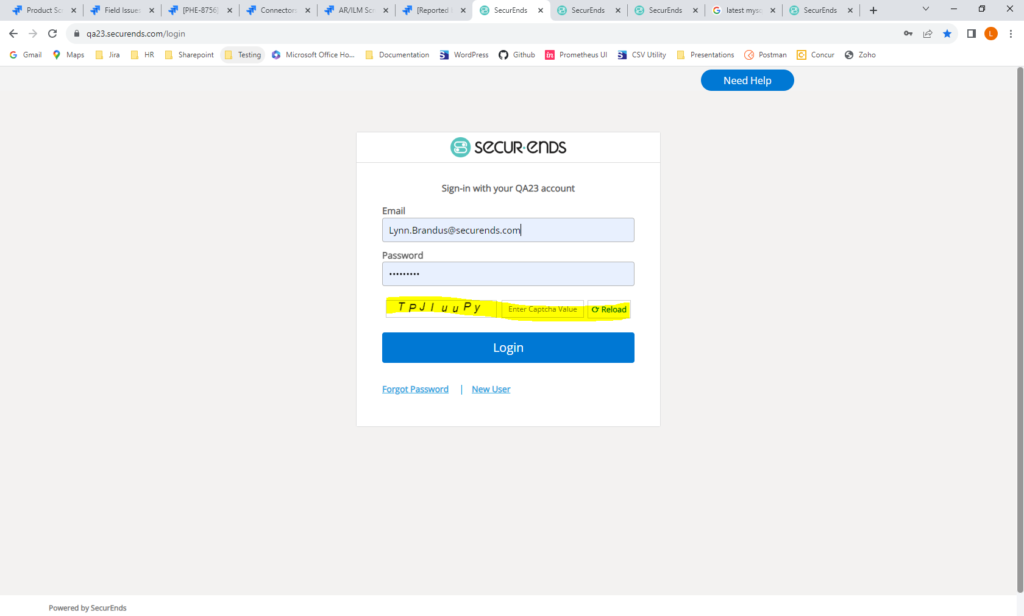
Added Captcha to Login Page
Campaigns
Added the Ability to Create Hierarchical Campaigns
This feature enhances campaigns by providing the ability to create multiple levels of approval. After the initial review process, the campaign may be reviewed by two additional reviewers before completing the campaign.
When each review level is 100% complete, the review will automatically be sent to the next level of reviewers. The 2nd or 3rd level reviewers may be the Direct Manager (if not reviewed by Direct Manager at the 1st level), Reviewer’s Manager or an Alternate Reviewer. The 2nd and 3rd level reviewers will see the elections made by the previous reviewer. They may choose to keep the election made by the previous reviewer or change it. Once a campaign level is complete, it moves to the next level reviewers. The previous reviewers may not view the campaign at that point. 2nd and 3rd level reviewers will be notified via email when the previous level is complete and the campaign is ready to be reviewed at their level. 2nd and 3rd level reviewers must select “Complete Campaign Level” on the Open Campaigns page when they have completed elections. When all reviewers have selected “Complete Campaign Level”, the review will move to the next level reviewers.
Administrators will have the ability to move the campaign to the next level of reviewers, even if the elections are not 100% complete.
To create a Hierarchical Campaign, navigate to Campaigns->Add.
Select the first level campaign reviewer.
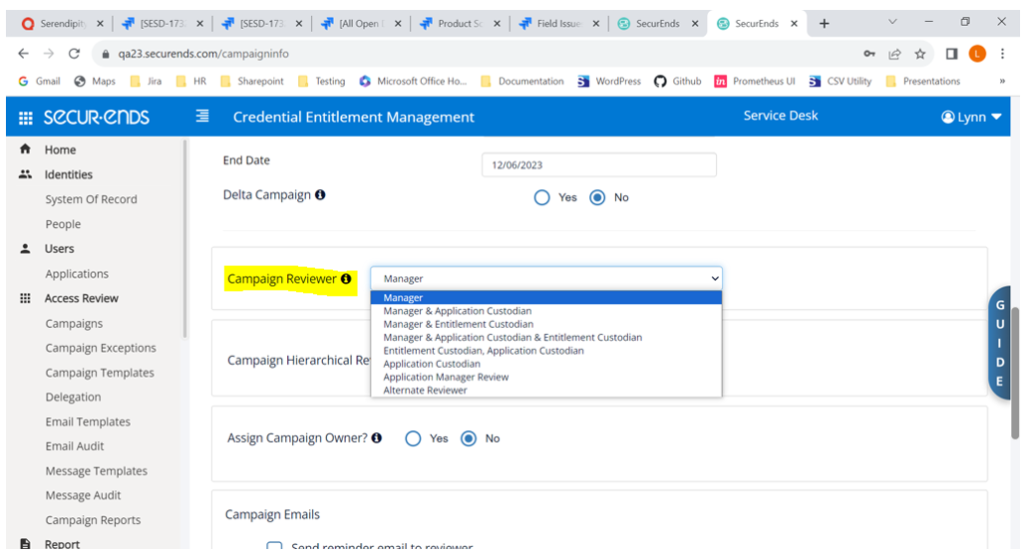
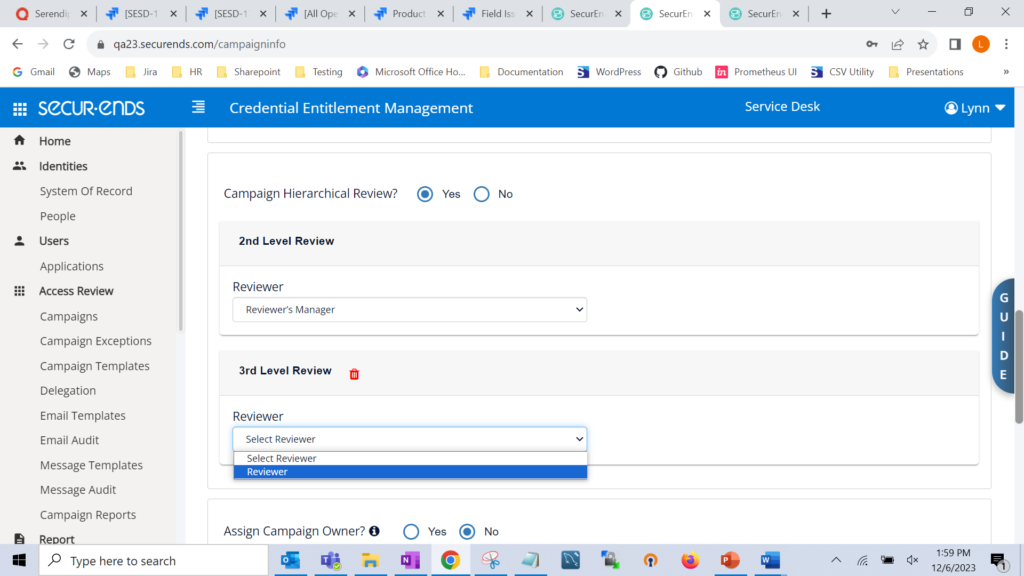
Select Hierarchical Review = Yes, and select the 2nd level reviewer.
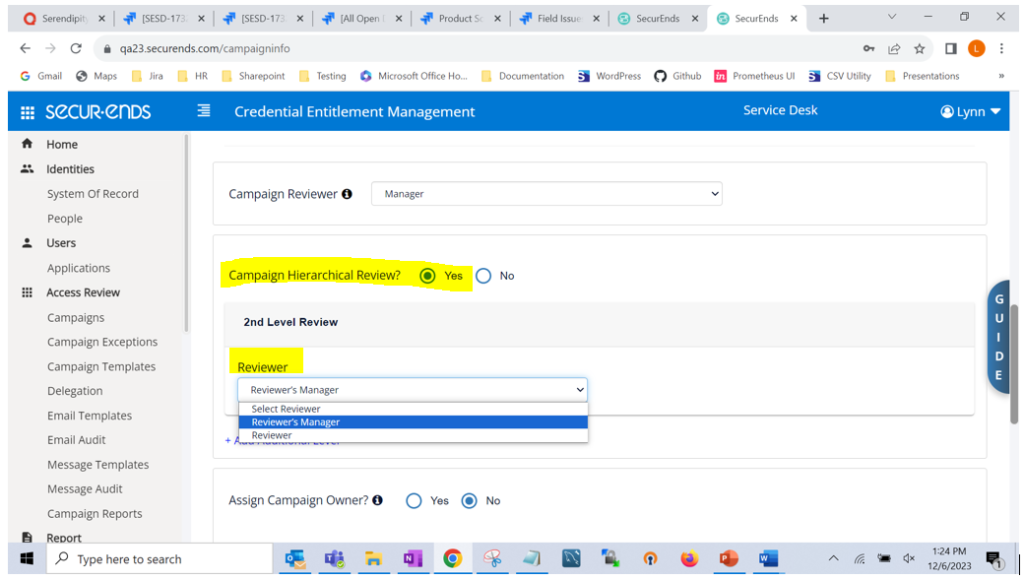
To select a 3rd level reviewer, click “+ Add Additional Level”
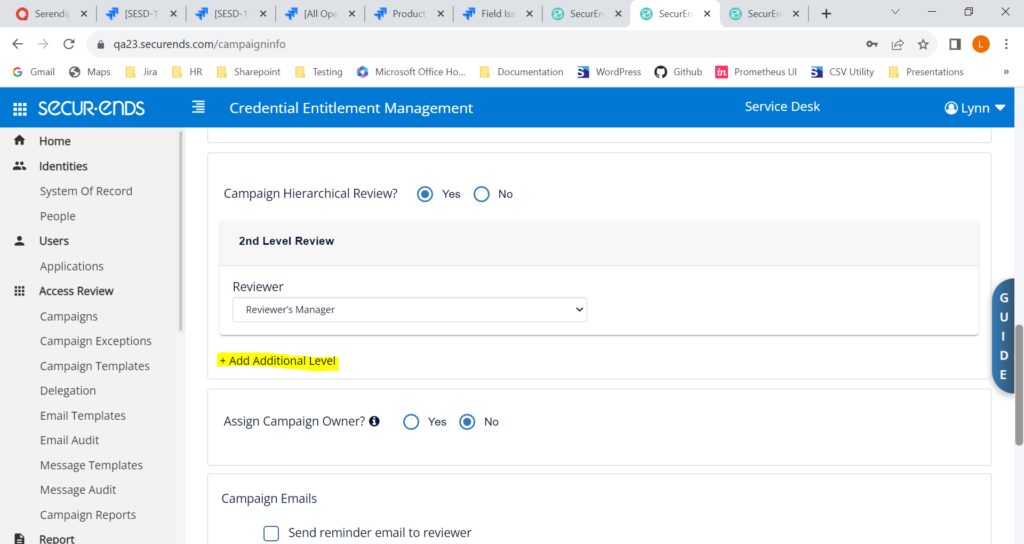
Select a 3rd level reviewer.
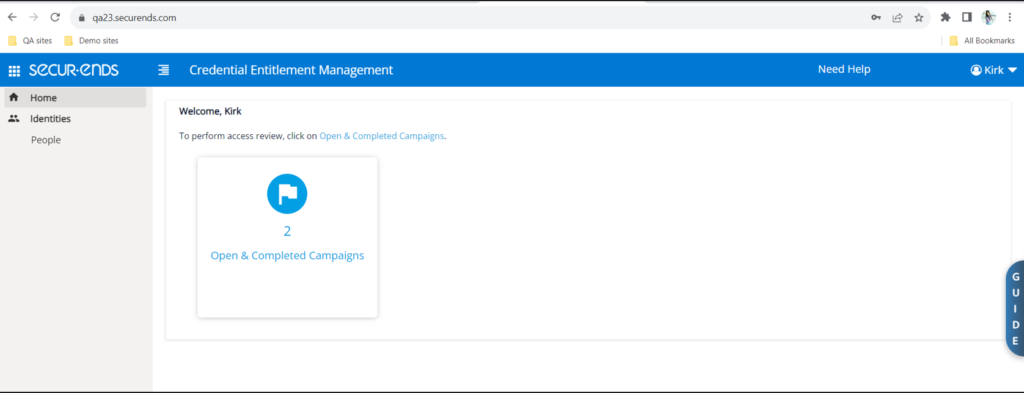
Reviewers will see the hierarchical review by clicking “Open & Completed Campaigns”
To perform the review, reviewers select “Continue Review”.
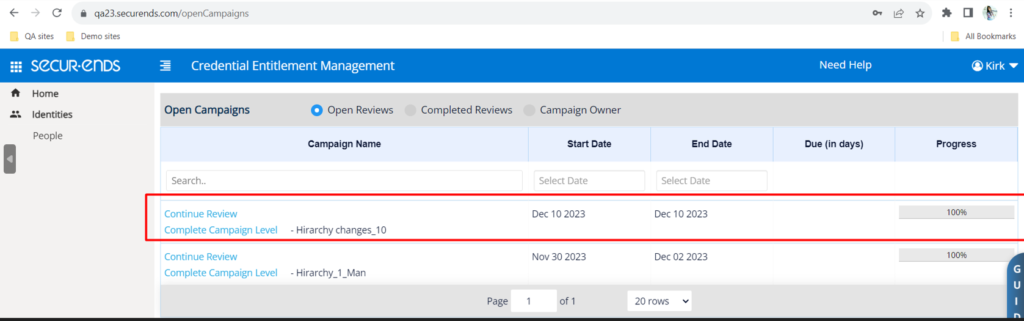
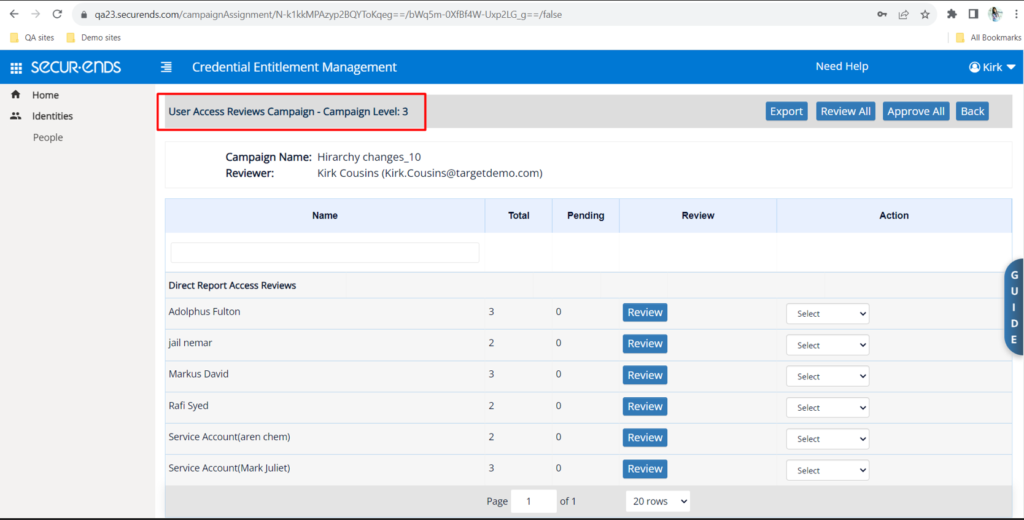
When all elections are made, the Reviewer should select “Complete Campaign Level”. When all Reviewers have completed the level, reviews will automatically be sent to the next level Reviewers.
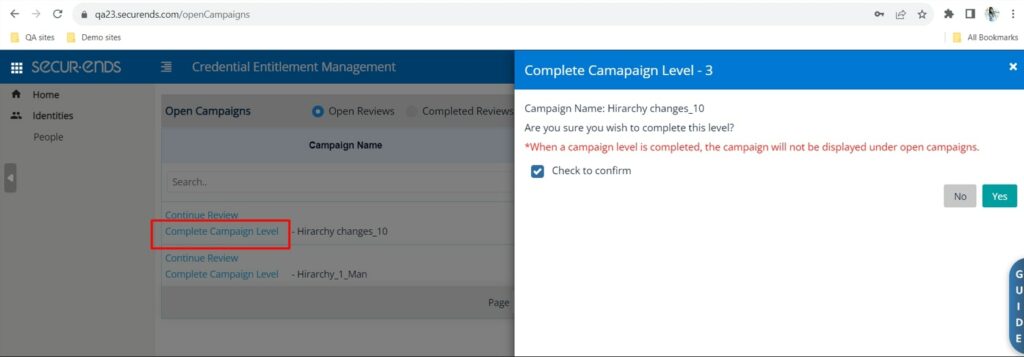
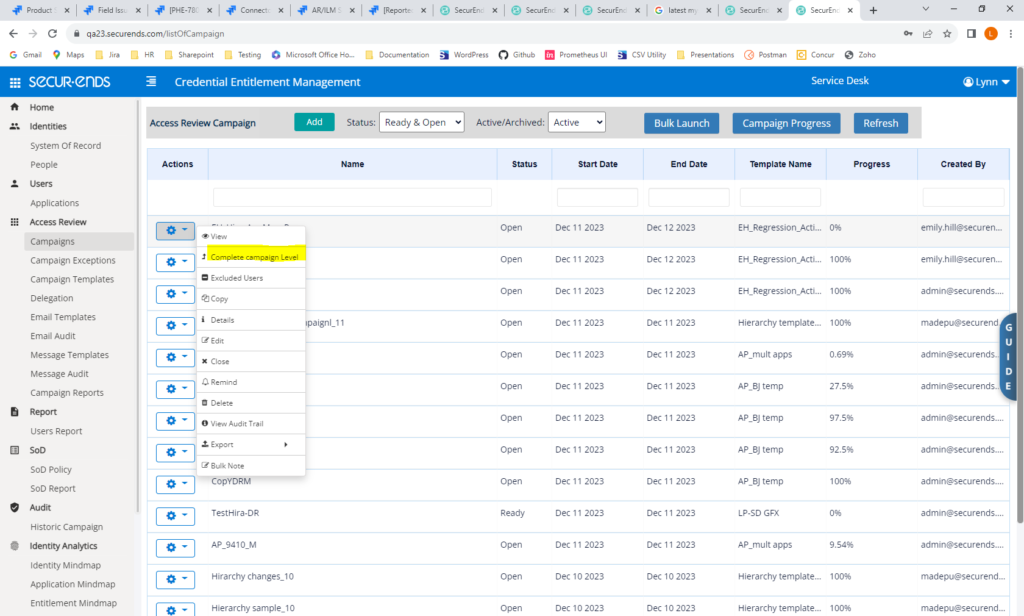
Administrators may select “Complete campaign Level” on the Campaigns action gear to move to the next level even though all reviewers have not selected “Complete Campaign Level” and elections are not complete.
Added the Ability to Send Additional Escalation Emails to Upper-Level Management
When reviewers have not completed reviews by the end date, an escalation email may be sent to their direct manager. We have added the ability to also send an additional email to the manager’s manager or anyone else when the reviews are not complete.
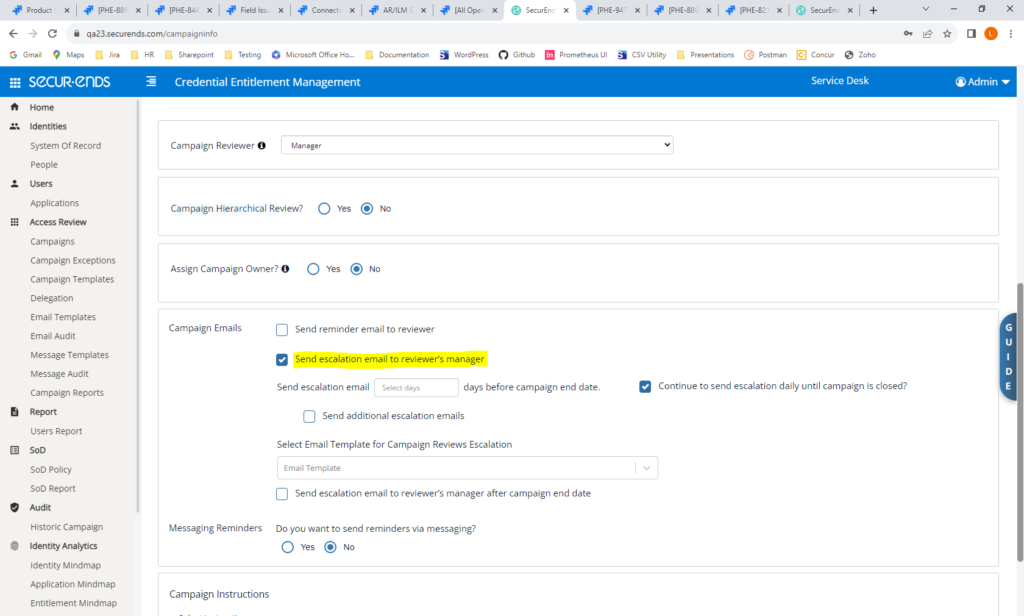
Navigate to Campaigns->Add. Select “Send escalation email to reviewer’s manager”.
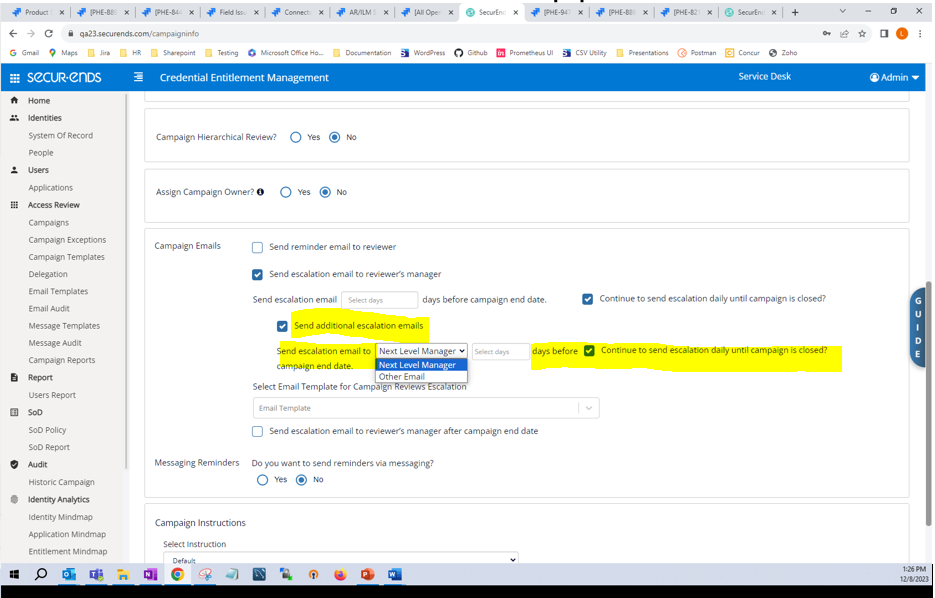
Check “Send additional escalation emails”. Select to send email to the next level manager or another person. Also select when to send the email based on the number of days before the end date.
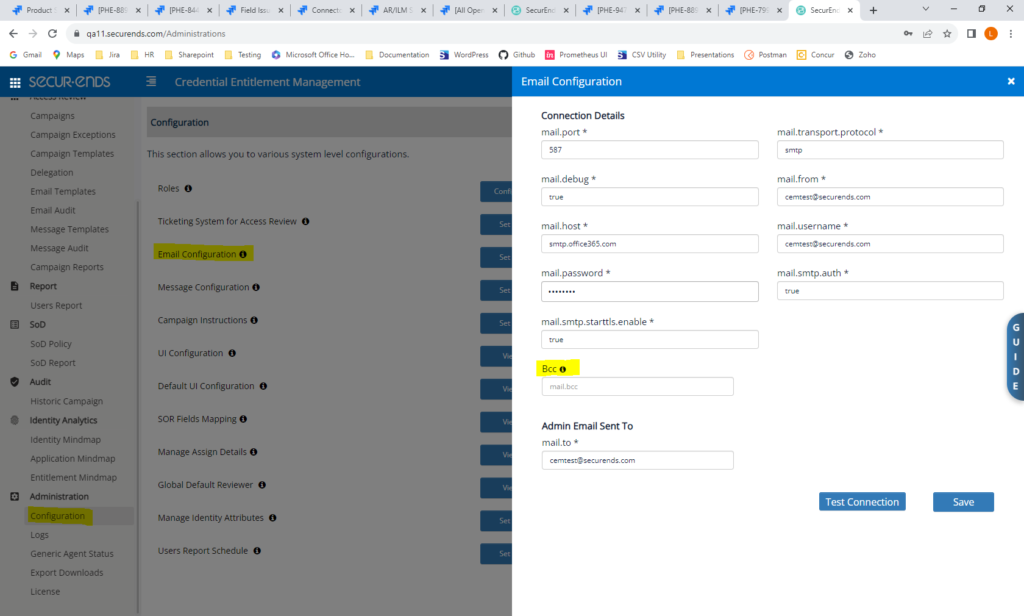
Added the Ability to Include BCC in Emails
We have added the ability to add a blind carbon copy in all emails. When the BCC field is entered, all emails sent from SecurEnds will also be sent to the BCC.
Navigate to Configuration->Email Configuration->Setup. Add an email address in the BCC field.
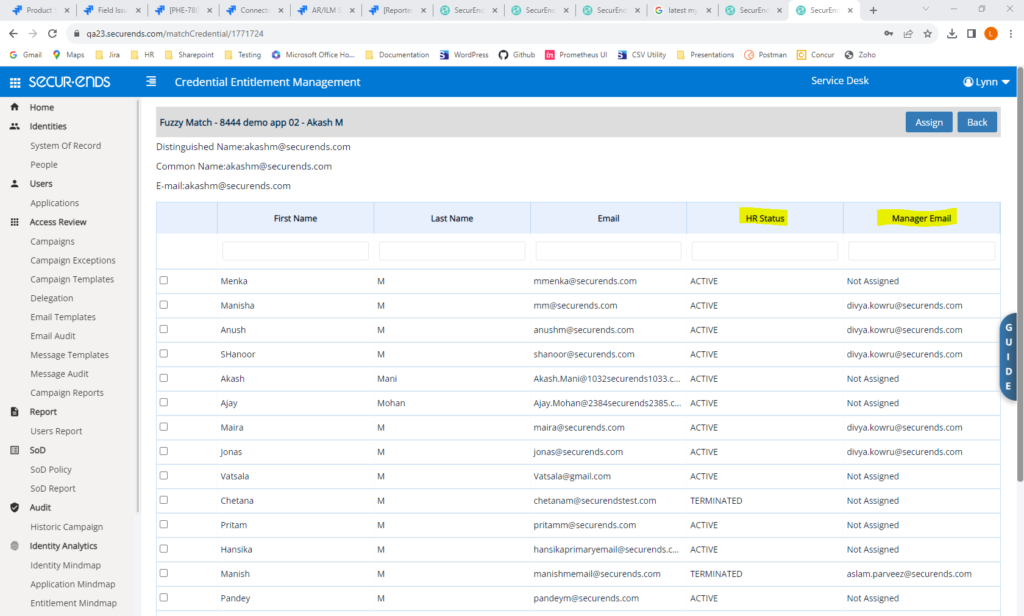
Added Fields to the Fuzzy Match Page
On the Fuzzy Match page, SecurEnds is now displaying columns for HR Status and Manager Email.
Navigate to Applications->Credentials->Unmatched Credential->Match
Applications
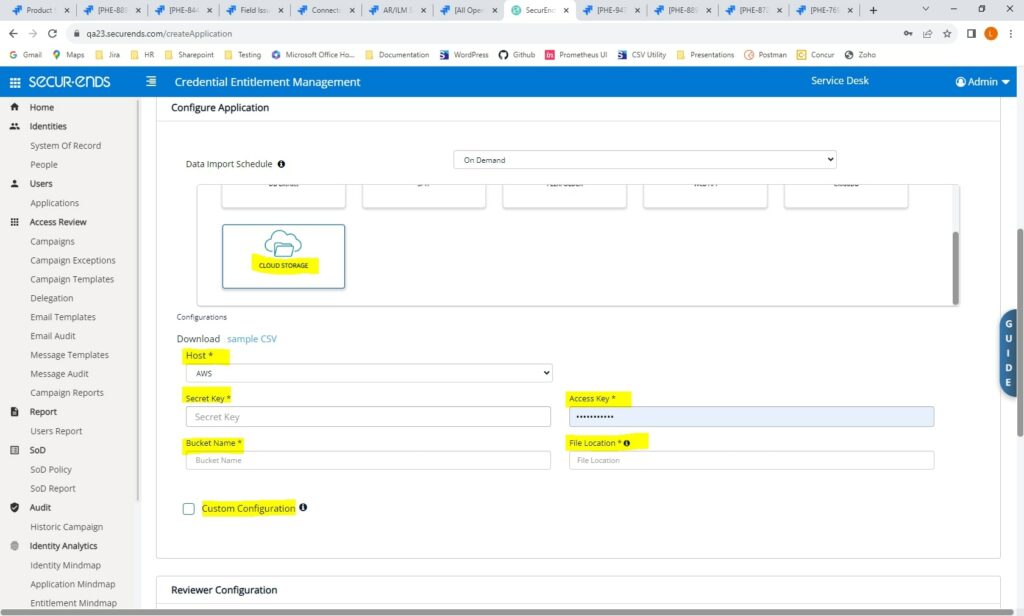
AWS Cloud Storage Connector – New Connector
We have created a new connector to expand the SFTP connector capabilities. This new connector gives users the ability to use SFTP but connect to an AWS file repository.
Navigate to Applications->Add->Data Ingestion = Flex Connector.
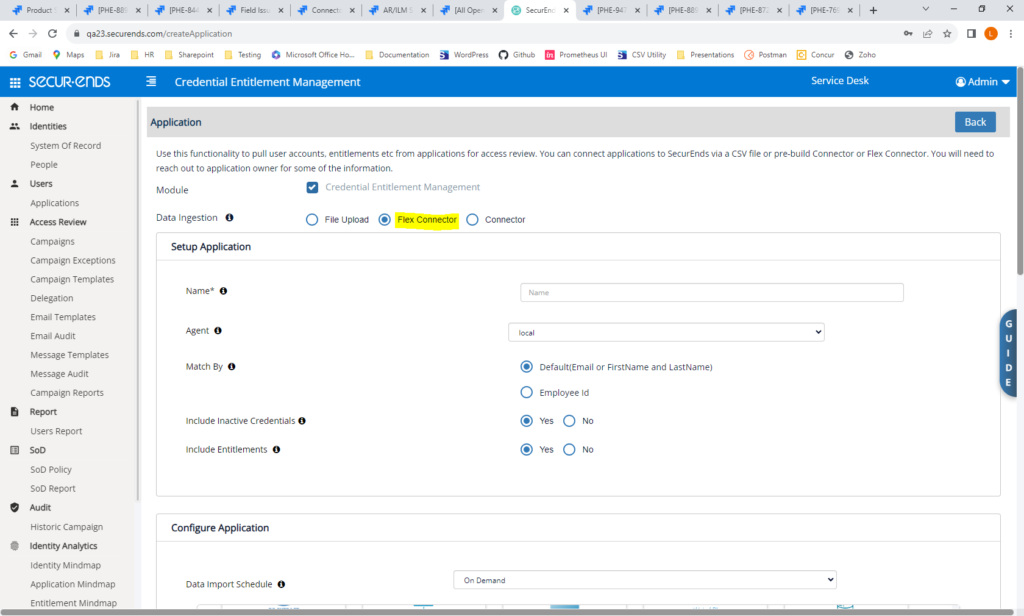
Select Cloud Storage and add connection details and mapping.
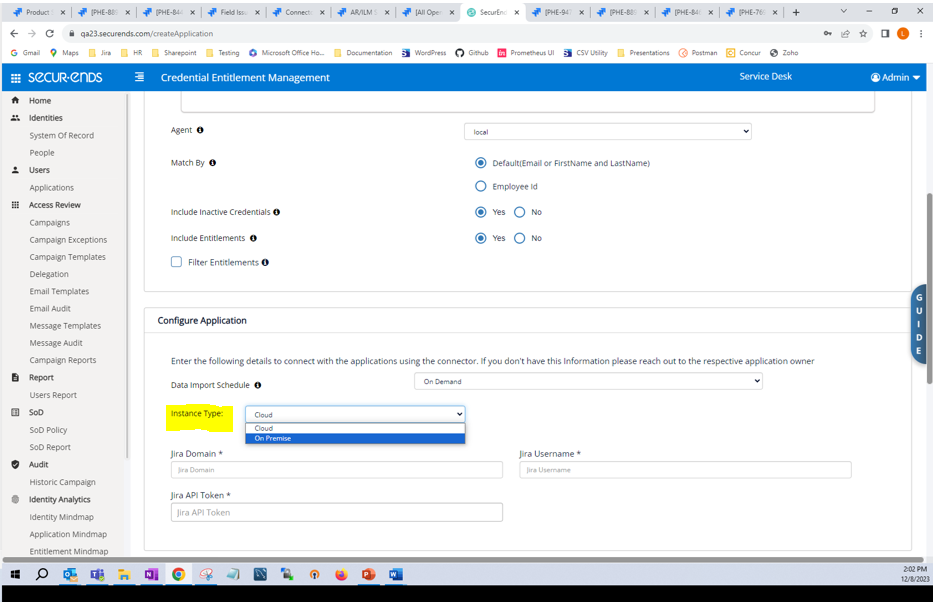
On-Prem Jira Connector – New
SecurEnds now supports On-Prem Jira.
Navigate to Applications->Add->Data Ingestion = Connector. Select Jira.
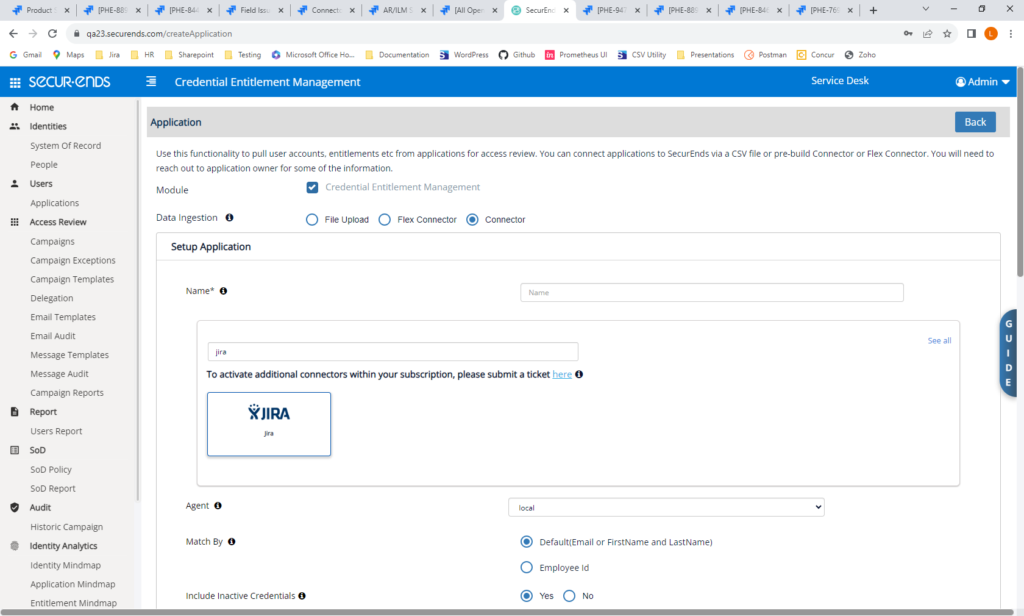
In Configure Application, select Instance Type = On Premise. Add connection details and mapping.
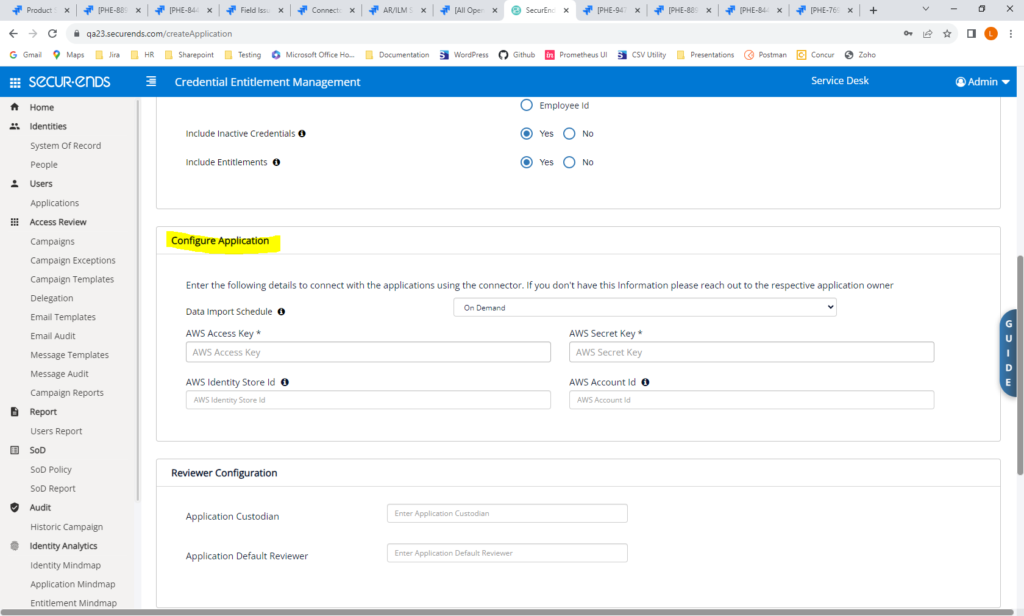
AWS IAM Identity Center Connector – New
SecurEnds has built an AWS IAM Identity Center/AWS SSO Connector. Any SSO may be configured to add users and groups to the AWS IAM Identity Center. SecurEnds will pull users as credentials and groups and permission sets as entitlements from the AWS IAM Identity Center.
Navigate to Applications->Add->Data Ingestion = Connector. Select AWS IAM Identity Center.
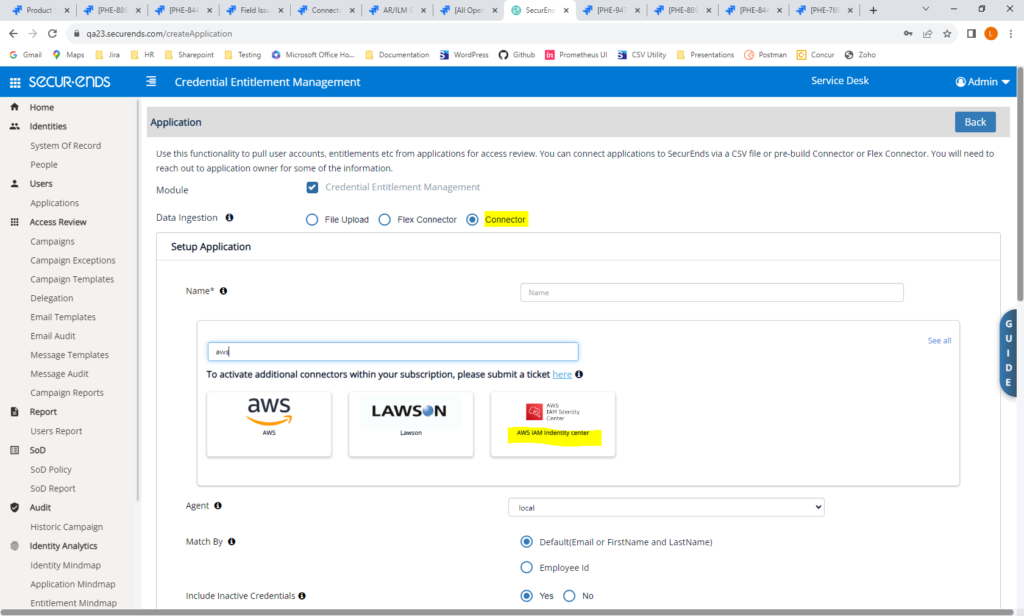
Add connection details under Configure Application.
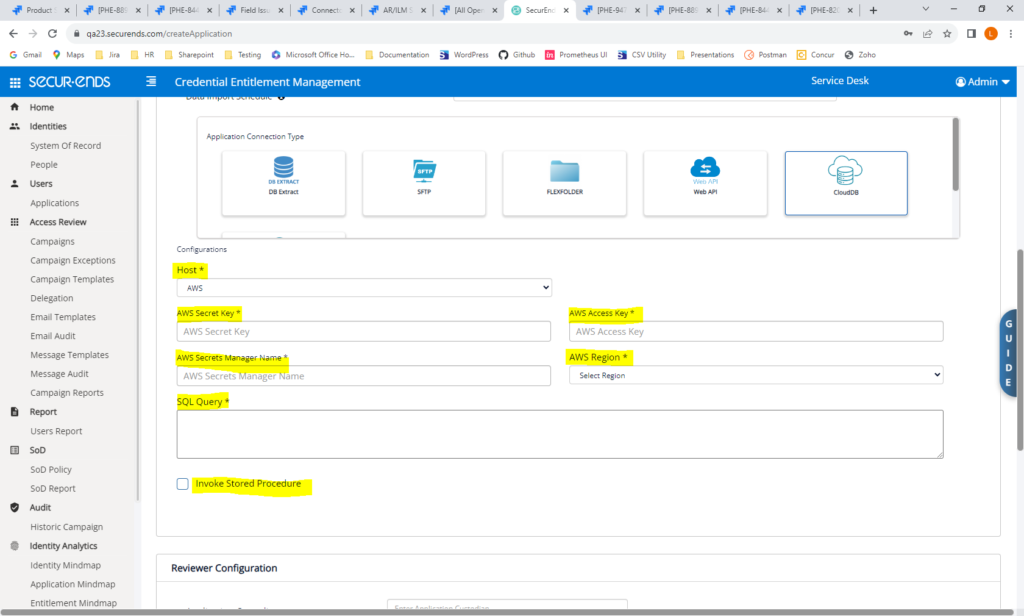
AWS Cloud DB Connector – New
SecurEnds has added a new connector to pull from an AWS Cloud DB. This connector will utilize an access token for authentication.
Navigate to Applications->Add->Data Ingestion = Flex Connector. Select Cloud DB.
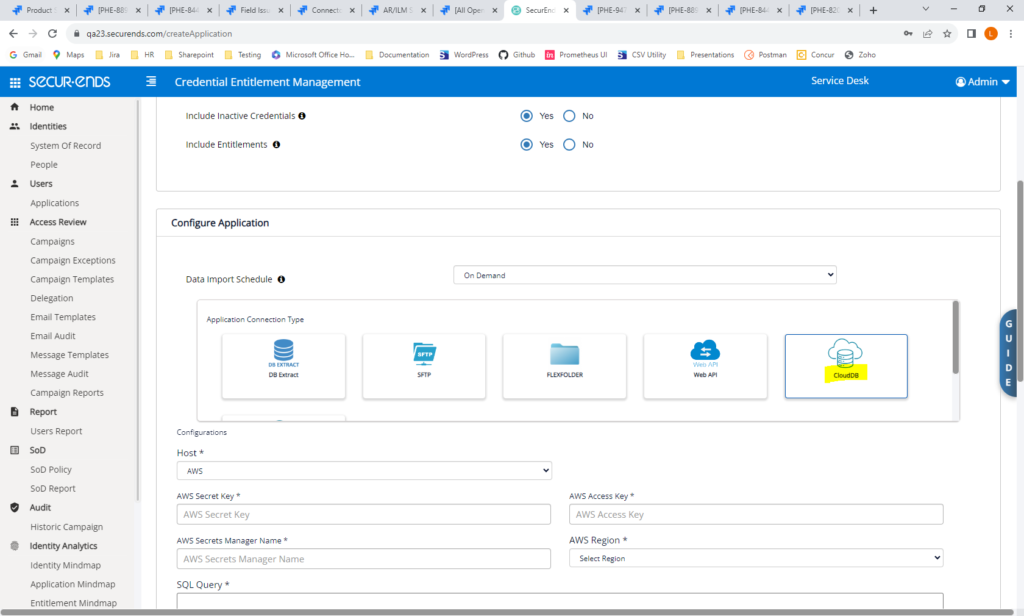
Add connection details.
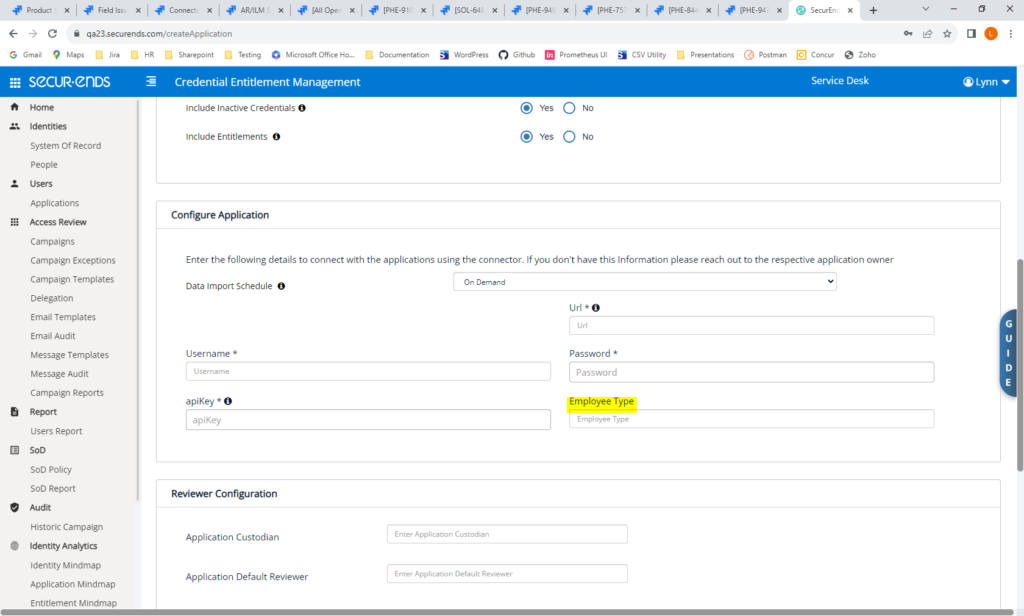
Ultipro (UKG) Connector – Updated
Improvements have been made to the Ultipro(UKG) Connector. Tooltips were added to the Configuration label.s and Last Authentication Date is now displayed. Role and it’s description details are shown on the Application Entitlement page. Employee Title, Job Title and Department with their associated descriptions are shown on the People page. We have added the ability to map employeeType to any key by specifying it in the Configure Application section.
Navigate to Applications->Add->Data Ingestion = Connector. Select Ultipro.
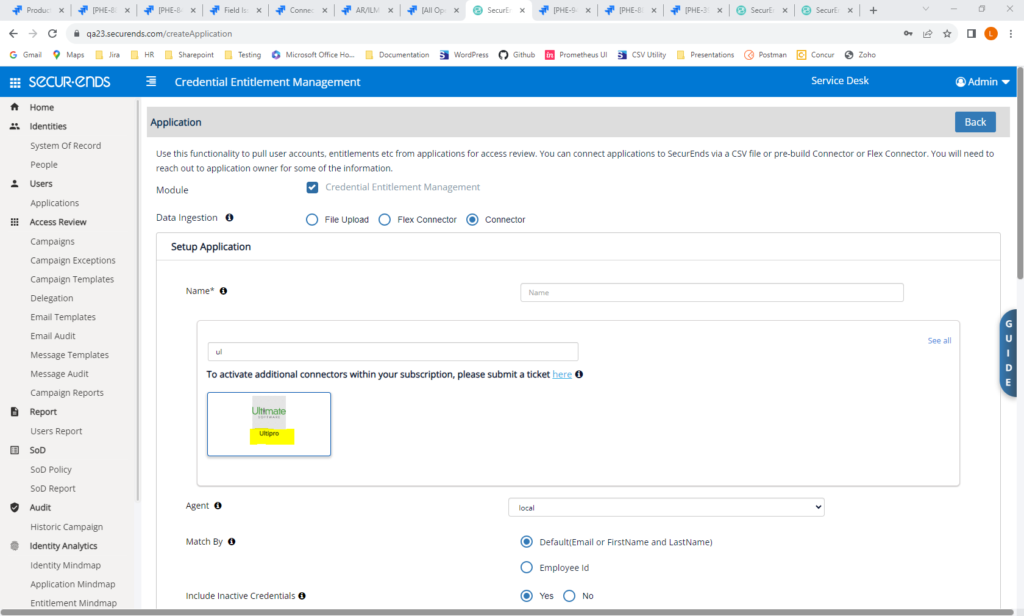
Enter connection details.
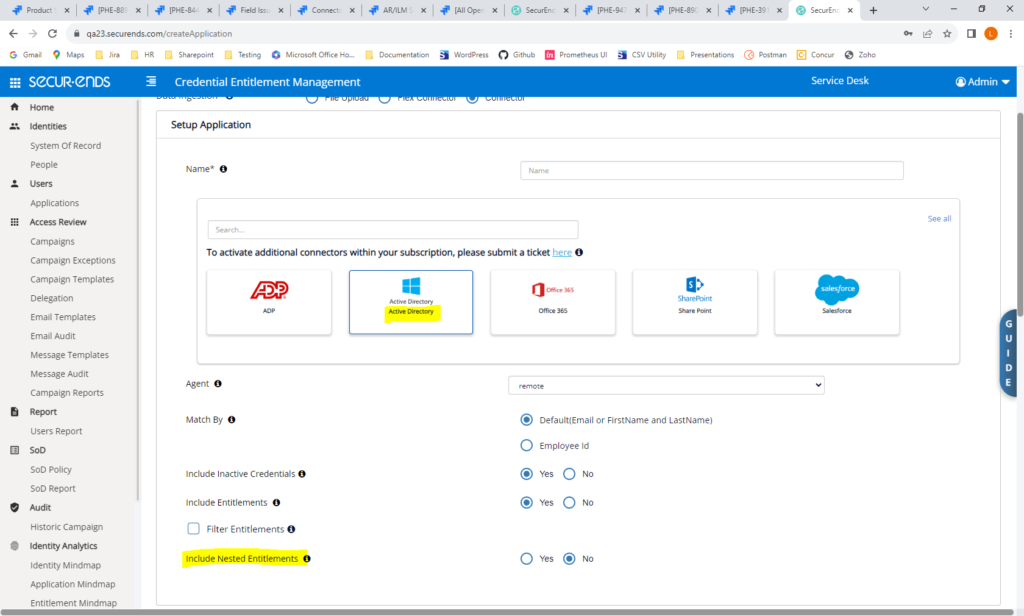
AD Connector – Show Nested Entitlements by Default
For the AD Connector, SecurEnds will always show “Include Nested Entitlements” with a default of No. Previously, in order to include Nested Entitlements, the DevOps team needed to set a DB configuration.
Navigate to Applications-> Add->Data Ingestion = Connector. Select Active Directory.
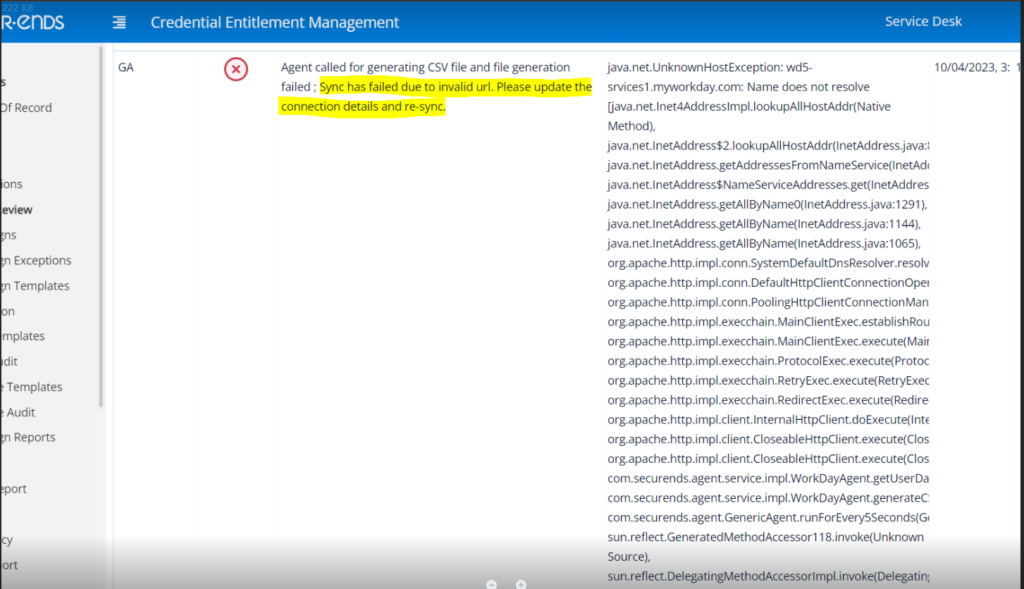
Workday Connector – Improved Failure Messaging
When there was a failure in the Workday sync, a generic message was displayed in the log file. A more informative message will now be displayed in the logs when there is an invalid url, invalid username or invalid password.
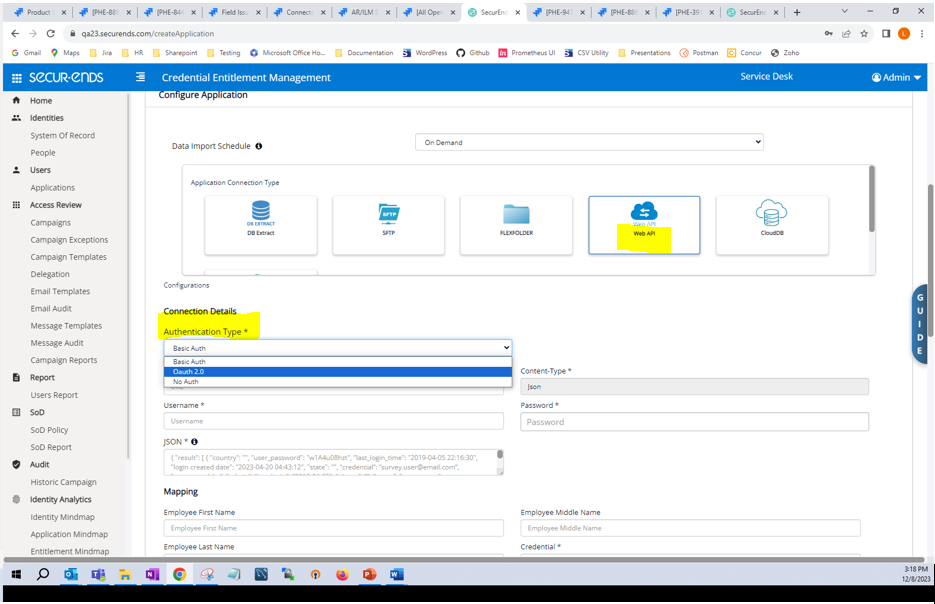
WebAPI Connector – Added Support for Oauth 2.0
The WebAPI Connector was added in our last release. In this release, we have added authentication using Oauth 2.0.
Navigate to Applications-> Add->Data Ingestion = Flex Connector. Select WebAPI. Select Authentication Type = Oauth 2.0.
Access Request/Identity Lifecycle Management
Added a Configuration to Be Able to Request Access for Any Application, Regardless of Group Assignment
In the Request Access module, users are able to request access for applications that apply to user groups they are included in. With this feature, we have provided the ability to request access to any application, regardless of user group. This feature is configurable.
Navigate to Configuration->Default UI Configuration. Search for RESTRICT_REQUESTS_BY_USER_GROUP. To display applications for request based on User Groups, then set the configuration to “true”. To display all applications for request, regardless of User Groups, then set the configuration to “false”.
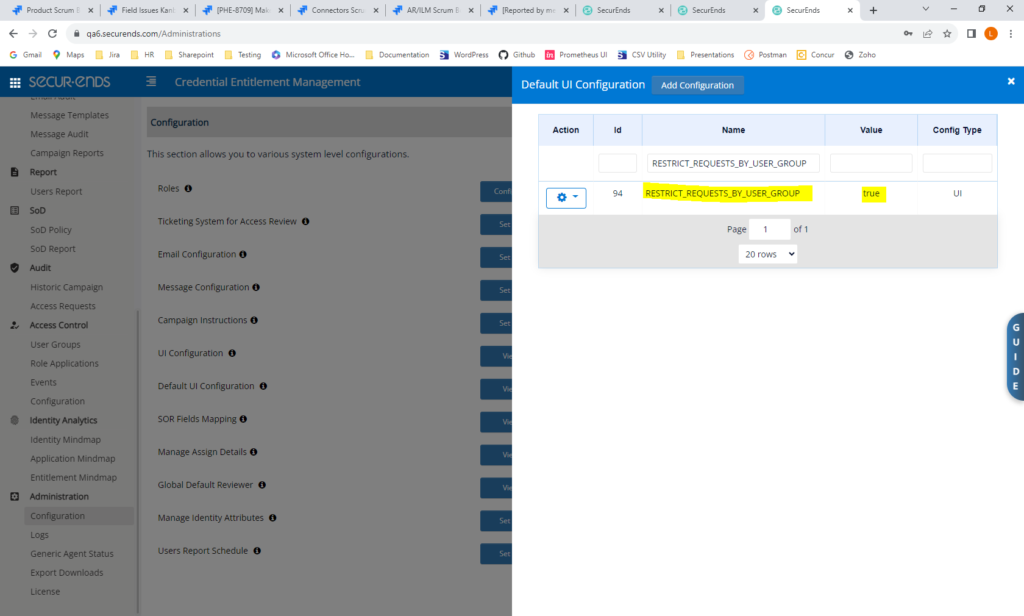
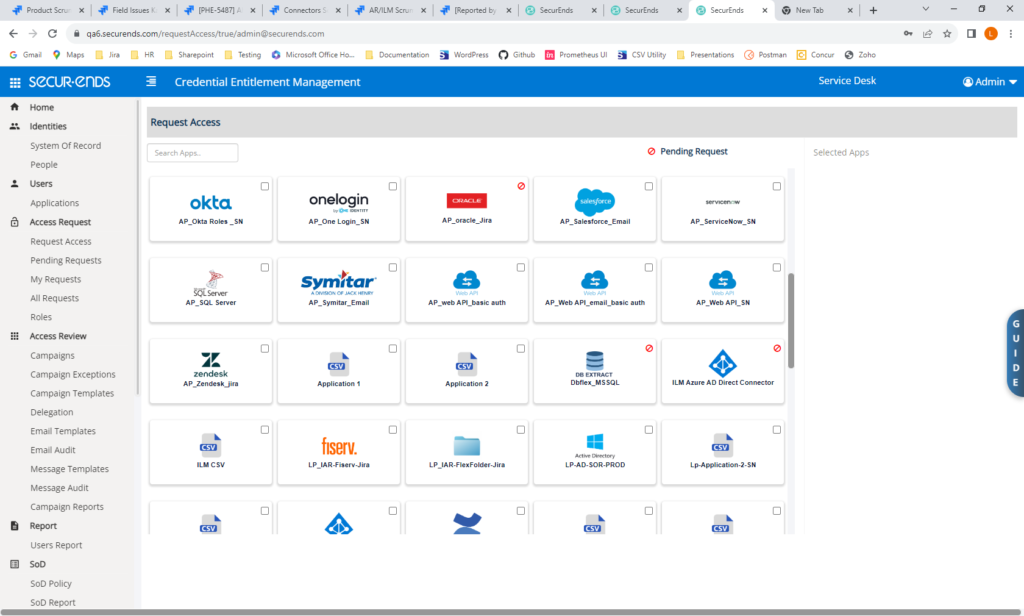
Navigate to Request Access. Available Apps will display for selection based on this configuration.

Improved Request Access UI
We have made minor UI changes to make the Request Access page more intuitive. The user’s current applications are displayed at the top under the “Your Apps” heading. Applications available for request are displayed under the “Available Apps” heading.
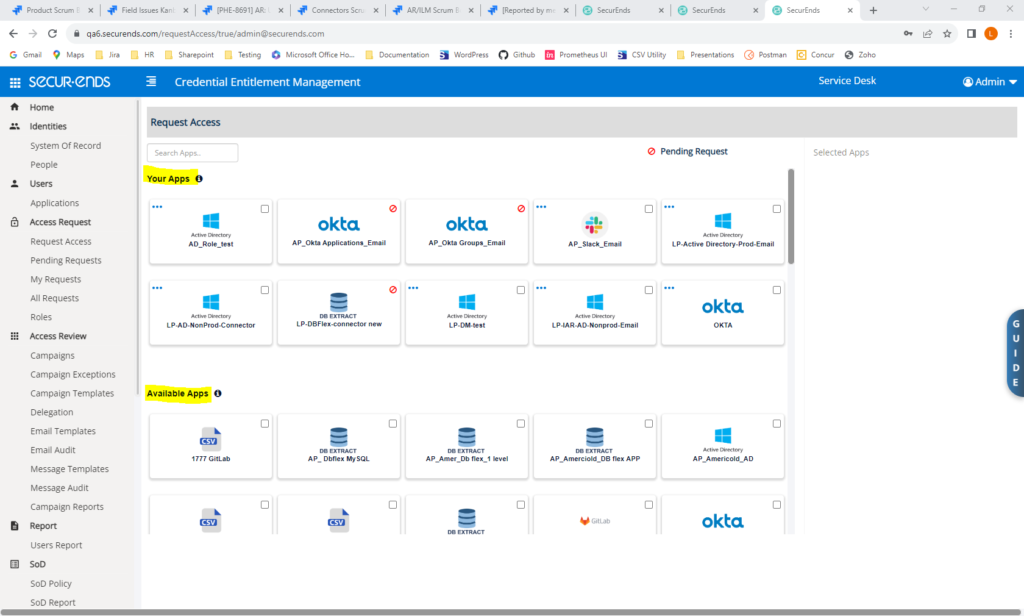
When an application is selected for request, it will be selected and specific roles and groups may be selected.
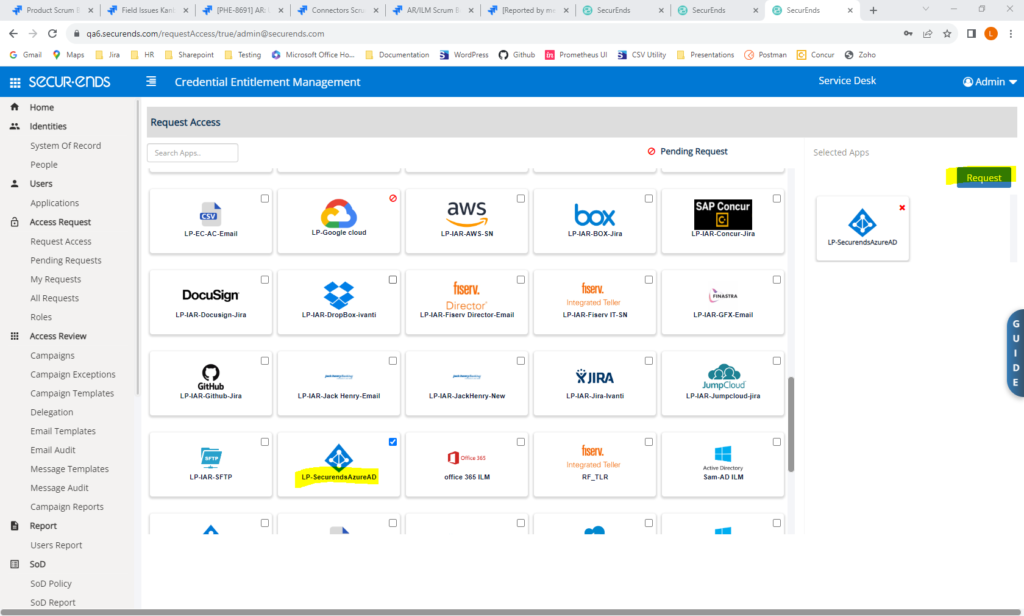
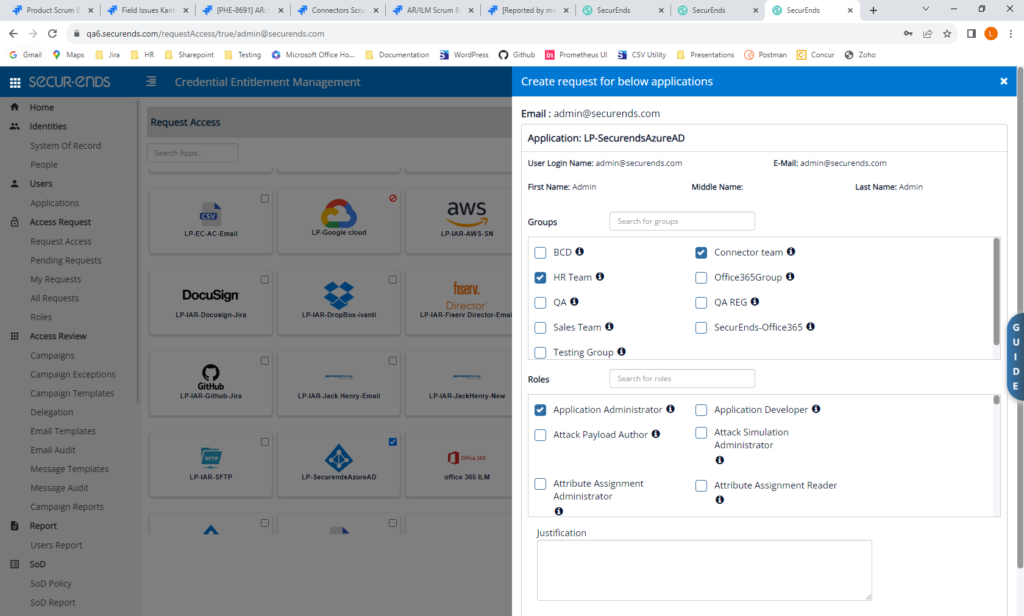
Added the Ability to Request All Application Types
Previously, users were only able to request access for applications set up as CSVs, DB Flex, Azure or Okta. We have added the ability to select any application type, including all DB Flex and all Connectors.
All application types may now be selected for request.
Audit Trail
Added an Audit Trail for Administration Configurations
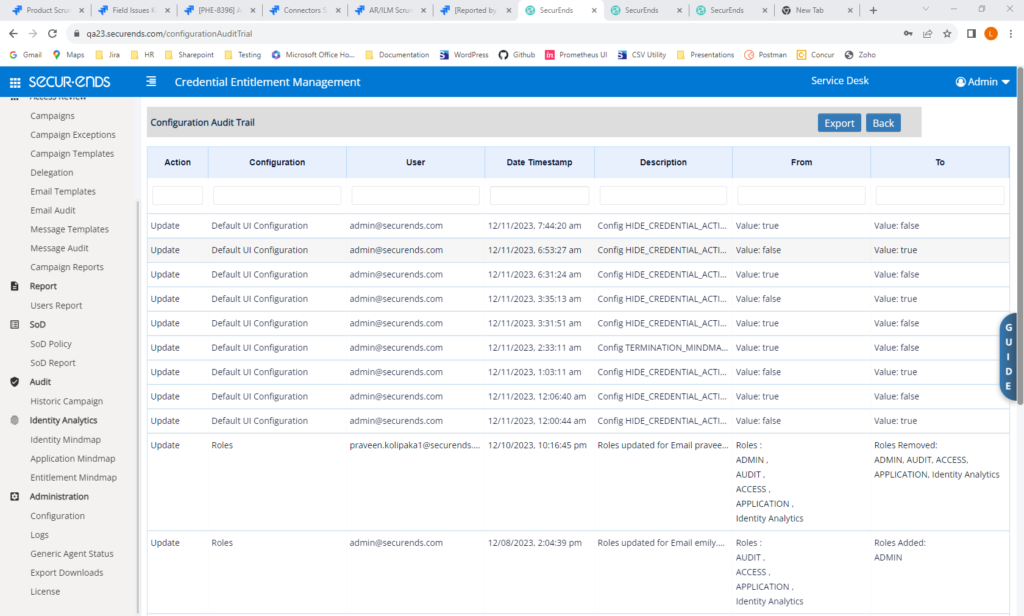
To keep administrators informed of which configurations have been changed and by who and when, we have added an Audit Trail to capture this information. This version of the Audit Trail will capture changes to Roles configurations, Ticketing configurations, Email configurations, Message configurations, UI configurations and Default UI configurations. Additional configurations will be added to the Audit Trail in future releases.
Navigate to Administration->Configuration. Click the “Audit Trail” button.
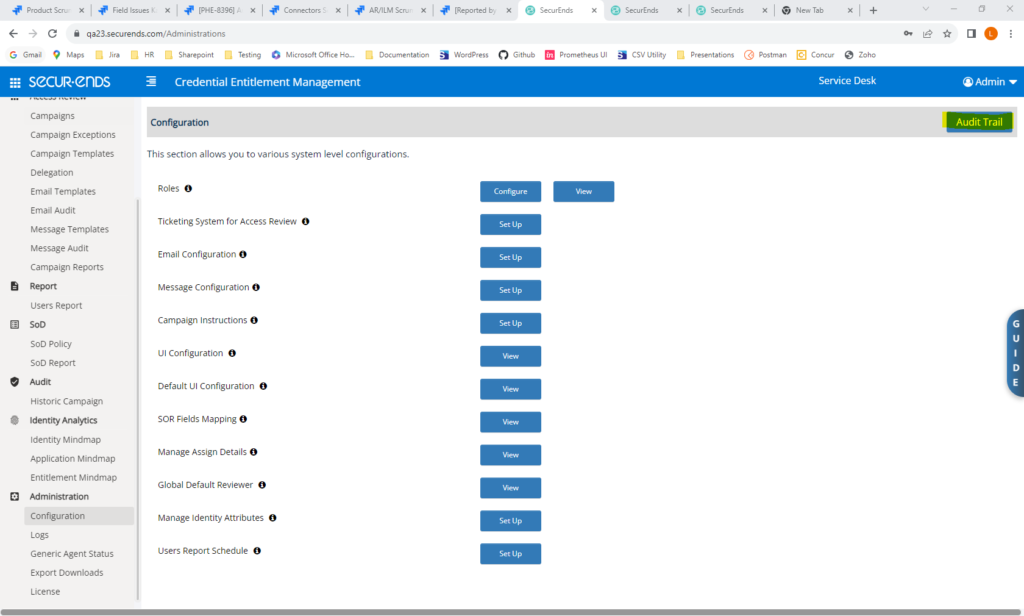
The Audit Trail will show which configurations have changed, who made the change, when the change was made and what the previous and new values are.
Ticketing
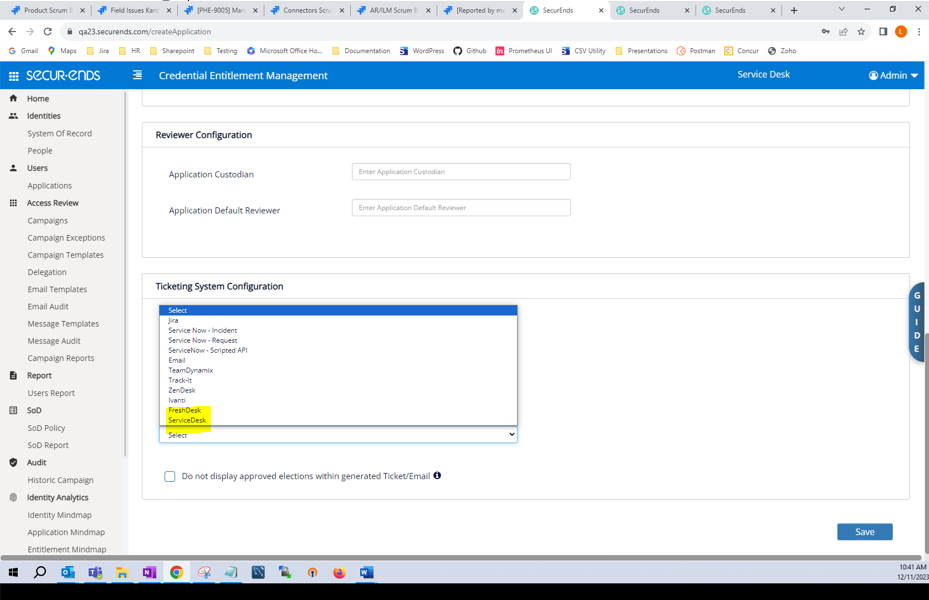
Added Ticketing for ManageEngine ServiceDesk
SecurEnds is now able to send tickets via ServiceDesk.
To configure ServiceDesk, navigate to Configuration->Ticketing System for Access Review. Select “Set Up”. Select “ServiceDesk” in Ticketing System dropdown and enter connection details.
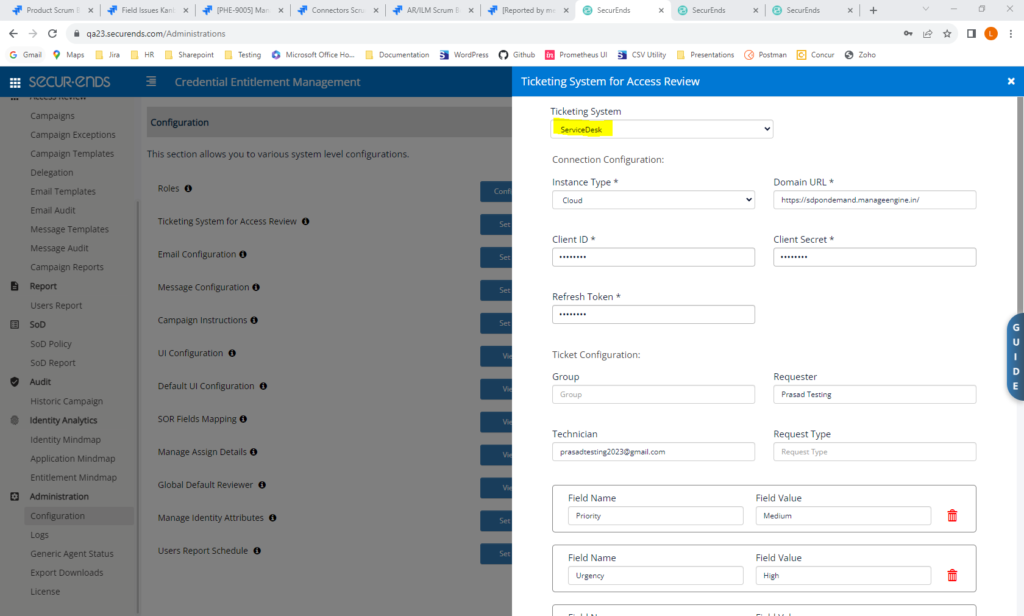
When setting up applications, select “ServiceDesk” for ticketing.
Added the Option to Use the Two-Step Checkout Model in Service Now Request
SecurEnds is now able to support ticketing for Service Now Request when customers have Two-Step Catalog Checkout Model enabled.
Security
Upgraded to Latest MySQL Version 8.0.34
Added Captcha to Login Page
SecurEnds has implemented SW patching to ensure resiliency and security and improve performance.
Captcha on Login page for username/pw login: