VIP Spoofing Prevention to Secure High Value Accounts
VIP Spoofing Prevention to Secure High Value Accounts
Prevent targeted VIP attacks and safeguard your enterprise’s most critical identities.
SecurEnds shields high value accounts by consistently monitoring for impersonation attempts. It correlates potential attacks with account roles and access risk to ensure only legitimate communications reach VIPs. By acting priorly, we help enterprises prevent costly breaches and maintain executive trust.
- Detect VIP spoofing attempts in real time before delivery
- Block impersonation attacks targeting executives and privileged users
- Prioritize response based on identity exposure and risk context
When VIP Accounts Are Spoofed, the Stakes Are High
Modern attackers are targeting executive and high privilege accounts with highly convincing spoofing campaigns. These attacks often bypass SPF, DKIM, and DMARC checks, making emails appear legitimate while tricking employees into sharing sensitive information.
Without identity focused visibility, security teams cannot quickly assess which VIPs are targeted and which accounts have elevated privileges. This creates blind spots which can result in rapid lateral movement, unauthorized access to critical systems, and regulatory exposure.
Enterprises need proactive monitoring of identity risk and executive targeted attacks to reduce breach impact and maintain trust at the highest levels.
Modern VIP Spoofing Attacks Target Executives and High Privilege Accounts
Email Impersonation
Attackers craft emails that appear to come from executives or trusted VIPs. They will trick employees into transferring funds or approving sensitive requests.
Display Name Spoofing
Malicious actors use fake display names mimicking executives to bypass standard filters and deceive recipients into acting on fraudulent instructions.
Domain Spoofing
Fraudulent emails are sent from domains similar to corporate domains. This will make detection by traditional tools difficult while targeting high value accounts.
Compromised Account Forwarding
Attackers exploit previously breached internal accounts to send spoofed messages, leveraging internal trust for higher success rates.
Executive Targeted Social Engineering
Attackers combine spoofed emails with personalized social information about the executive or team to increase credibility and response likelihood.
Phishing for Privileged Credentials
Attackers trick executives into revealing MFA codes or admin credentials to gain access to critical systems.
Modern VIP spoofing is not about volume. It is about precision, identity, and privilege exploitation.
Why Traditional Tools Fail Against VIP Spoofing
Generic security tools miss targeted attacks. Spoofed VIP accounts can lead to financial and compliance impacts before detection. Modern protection needs to act on identity, not just content.
Traditional filters can’t see the risk hidden in high-value identities.
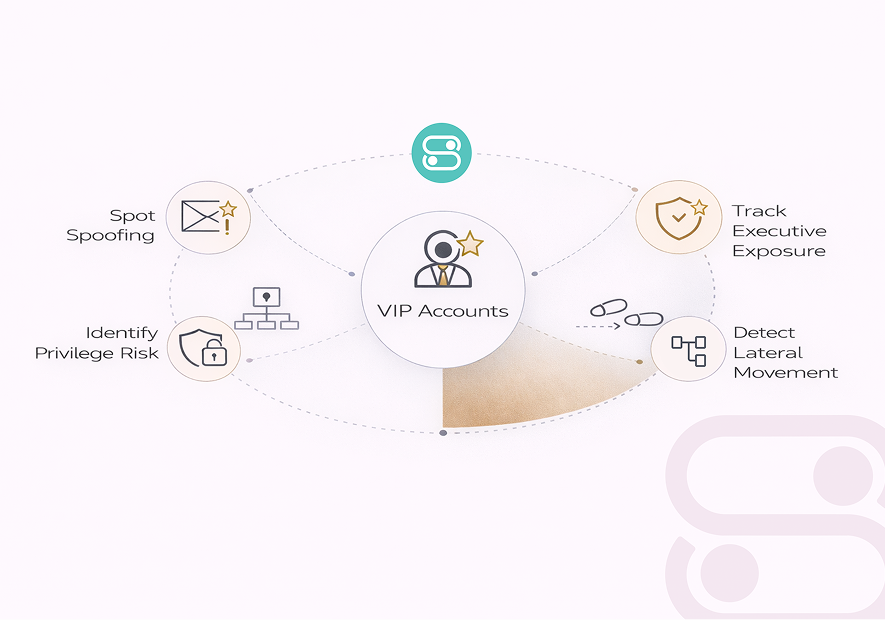
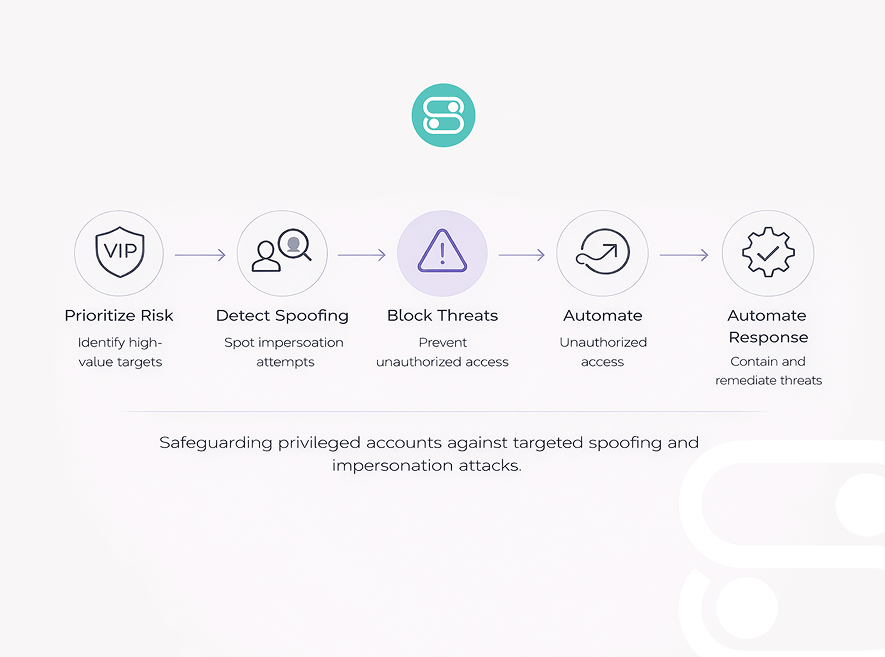
How SecurEnds Secures Critical Identities
Detect
SecurEnds identifies potential spoofing attempts targeting executives and high risk users in real time. Early detection ensures attacks are flagged before harm occurs.
Correlate
Signals are mapped to account roles and privileges. So security teams understand which VIPs are targeted.
Prevent
Compromised or high risk identities are isolated. Suspicious messages will be blocked from reaching inboxes.
Remediate
Security teams are guided to take immediate actions. Reset credentials, revoke sessions, and contain any potential exposure.
SecurEnds acts where email filters fail, at the level of roles and privileges.
VIP Spoofing Defense Built for Privileged Users
SecurEnds goes beyond email scanning to protect executive and high privilege accounts from targeted spoofing. By consistently monitoring identity context and account behavior, security teams gain actionable visibility.
High value accounts are secured before attackers can escalate privileges or exfiltrate sensitive data. SecurEnds ensures VIP protection is automated and aligned with enterprise risk priorities.
Key capabilities
- Prioritizes which privileged accounts are at greatest risk
- Detects potential misuse of high value account access
- Identifies domain, display name, and targeted impersonation attacks
- Guides immediate containment and credential resets
Detect, block, and remediate targeted attacks before they escalate into breaches.
What to Do After a VIP Spoofing Attempt Is Detected
VIP spoofing is an identity risk involving trusted executive roles and privileged access paths.
Once impersonation is detected, security teams must quickly determine whether executive identities or downstream systems are exposed.
SecurEnds correlates spoofing indicators with identity attributes, access entitlements, and role sensitivity to surface real risk. This let the teams distinguish between brand spoofing noise and attacks targeting high impact users.
By mapping spoofed identities to access scope and business workflows, SecurEnds enables precise containment decisions. So, security teams can act with clarity before attackers exploit trust or escalate into broader compromise.
Identify Targeted VIPs
Confirm impersonated executive or privileged identities.
Validate Access Scope
Check financial and SaaS access exposure.
Restrict and Recover
Limit access and initiate identity remediation.
Compliance Ready Protection Against VIP Spoofing
VIP spoofing introduces direct risk to financial controls and regulatory accountability. Impersonated executives can unintentionally bypass governance safeguards if identity risk is not actively monitored.
SecurEnds helps organizations demonstrate proactive control over high risk identities with clear audit trails and response records. This strengthens compliance posture and reduces exposure to fraud and regulatory violations.
Compliance alignment
Audit-ready reports
Access change tracking
Proof of proactive risk mitigation
What Teams Say About Working with Us

Ananya Iyer,
Head of IAM & GovernanceWe were dealing with frequent executive impersonation attempts, and the SecurEnds team helped us bring clarity to how we respond. The collaboration was smooth, and the outcomes were visible very quickly.

Raghav Mehta,
Director - Information SecurityThey understood executive risk immediately and helped us set things up without overcomplicating it. It felt more like working with an extension of our security team.
Industries We Work With
SecurEnds works with enterprises across highly regulated and security sensitive industries. Our customers manage complex identity landscapes with thousands of users and privileged accounts. We collaborate with security, IAM, and compliance teams at enterprise scale.
Why Enterprises Choose SecurEnds
SecurEnds is built for enterprises which treat identity as a core security control. Our platform helps teams manage identity risk with precision and operational confidence.
Identity First Security Architecture
Designed to protect high value accounts and privileged users across the enterprise.
IAM & IGA Alignment
Smoothly integrates with existing identity and governance systems for end to end visibility.
Cloud and SaaS Ready
Scales across distributed users and modern SaaS environments without added complexity.
Zero Trust Security
Consistently validates access and reduces standing privileges across sensitive workflows.
SecurEnds helps enterprises protect what matters most – trusted identities and critical access. It is identity security built for real world scale and accountability.
Frequently Asked Questions
It focuses on protecting high value accounts and executive identities from impersonation attacks. Standard tools often miss targeted spoofing attempts.
No. It complements your current email security by adding identity focused protection for VIPs and sensitive roles.
Yes. It detects malicious impersonation attempts even when email passes standard authentication checks.
Alerts are generated in real time. This will let teams to act immediately on suspected spoofing or impersonation attempts.
Absolutely. It works alongside IAM, IGA, and SIEM for coordinated detection and response.
It can protect high privilege users and any account flagged as critical, ensuring broader enterprise coverage.
Prevent Spoofing Before It Reaches Critical Accounts
Detect targeted spoofing in real time and prevent attacks from escalating into full scale breaches. Stay ahead of attackers and secure critical identities across your enterprise.


