User Access Reviews : Enabler For Digital Transformation
User Access Reviews : Enabler For Digital Transformation

Digital Transformation Requires Security Transformation
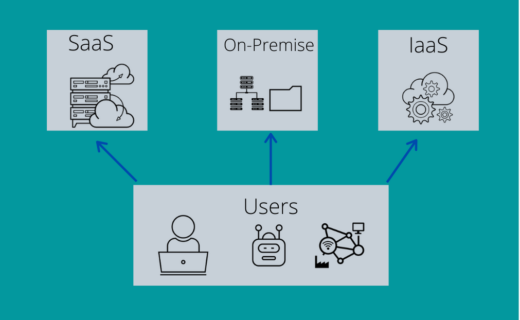
Organizations are adopting a bring your own device (BYOD) approach to provide remote access to sensitive data, and business applications. Organizations are moving applications and resources to the cloud as part of a broader digital transformation. Often times these organizations are operating a hybrid with multiple legacy applications running in on-premise or colocation data centers while other Software as a Service (SaaS) applications running in cloud Organizations are developing Internet of Things (IoT) and Robotic Process Automation (RPA) at a staggering rate.
Consequently, Securing access and managing identities is simply too important to treat as just a function of Access Management (Single Sign On, Multi Factor Authentication) and Privileged Access Management.
Single Sign On (SSO) Is The First Line Of Defense
SSO is the ability to authenticate once and never have to repeat the process for federated applications again in the session. It accords two benefits. Firstly, SSO eliminates the need to remember individual passwords allowing frictionless log in experience. Secondly, given identity management is being centralized, security team can control access to every application in one place.Most enterprises don’t have SSO implemented across its entire application sprawl comprising of on-premise and cloud applications. This leaves organizations at risk.
Access Reviews Promote Cyber Security
More and more organizations are using access reviews as a key enabler for their cyber security strategy. Why? User access reviews or attestations allow organizations to ensure users continue to have “least privilege” access. Assigning identities to devices makes it easier to control how and where employees access corporate networks, helping prevent some of the problems associated with establishing and enforcing BYOD/ IoT policies.Continuously monitoring privileges of users, cloud resources, bots, devices etc to ensure these identities have correct entitlements reduces the security risk and attack surfaces. As organizations scale, new users or devices request additional access either to new applications or to additional resources within applications. To maintain compliance with established controls, continuously monitor access requests to prevent compliance violations such as segregation of duties.Access reviews or attestations or role certification gained prominence with enforcement of standards such as Sarbane-Oxly(SOX), NIST, FDA 21 CFR etc. Simply put access reviews ensure right people have the right access to the right resources for the right reason at the right time. Many organizations continue to use a manual process where the user access list is sent to application owners for review, and users are removed as necessary. However, a growing threat landscape necessitates organizations to automate user access reviews to gain visibility into fine-grained entitlements and access privileges required to enforce compliance policy. An added benefit of automation is that it significantly reduces audit preparation costs, administrative burden and staff frustration. An easy to adopt automated user access review software will allow non-technical approvers to undertake user certification process.
Enter Micro-Certification
According to 2019 Insider Threat Report from Cybersecurity , 62 percent of organizations in 2019 year have experienced at least one insider attack. An effective way to handle insider threat is to do micro-certifications in conjunction with regular reviews. Micro certifications are event driven and are essential in managing a complicated landscape of user rights, permissions, and accounts. In many cases , these certifications can eliminate the need for full scale access certification processes saving organizations significant time and effort.
In summary the challenge for security teams remains how to add security at the speed of digital transformation.User access reviews provide a time tested method to flush out orphaned accounts that hackers use for malicious activities.


