Protect Your APIs from Authentication & Authorization Vulnerabilities
Protect Your APIs from Authentication & Authorization Vulnerabilities
Strengthen access control with advanced api authentication security, enforcing strict identity verification, token validation, and authorization policies across every API interaction.
Why Authentication & Authorization Are Critical
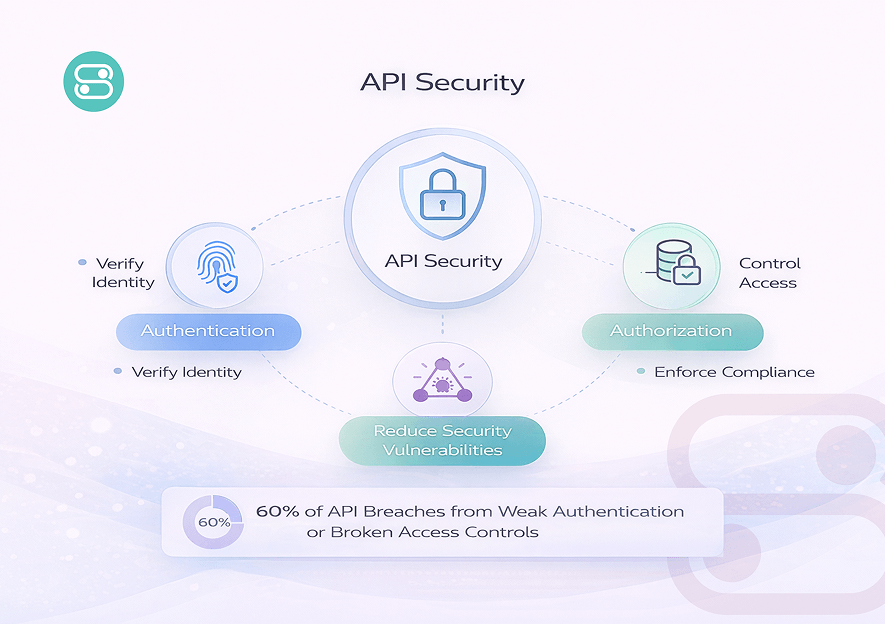
Authentication and authorization are two distinct but equally critical layers of API security. Weaknesses in either layer can have severe consequences.
- Authentication verifies the identity of a user, system, or application interacting with your API.
- Authorization determines the specific actions or resources that identity is allowed to access.
Without robust api authentication security, attackers can impersonate legitimate users, gain unauthorized access, or escalate privileges to sensitive systems.
Broken access controls can expose confidential data and enable fraudulent transaction. In fact, studies show that nearly 60% of API breaches are caused by weak authentication and broken access controls, making these vulnerabilities a leading source of API risk.
Properly implemented authentication and authorization prevent unauthorized access and also enforce compliance with regulatory requirements. It also helps maintain data integrity and build trust with users by ensuring API interactions remain secure and predictable.
Common Authentication Vulnerabilities
Weak Passwords or Predictable API Keys
Using simple passwords and predictable API keys makes APIs easy targets for attackers. Implementing strong api authentication security reduces the risk of unauthorized access through credential guessing or brute-force attacks.
Missing or Broken Authentication Mechanisms
APIs without properly configured authentication leave endpoints exposed to unauthorized users. Ensuring every endpoint enforces identity verification is critical to maintaining API integrity.
Token Flaws (JWT/Session Issues)Token Flaws (JWT/Session Issues)
Incorrectly implemented JWTs or session tokens can be manipulated to bypass security controls. Validating tokens properly and monitoring their lifecycle prevents exploits and maintains secure API interactions.
Lack of MFA or 2FA
Relying solely on passwords increases vulnerability to credential theft and account takeover. Integrating multi factor authentication or two factor authentication strengthens verification and protects sensitive API resources.
Common Authorization Vulnerabilities
Broken Access Control
APIs which fail to enforce proper access rules allow attackers to access resources they shouldn’t. Issues like BOLA (Broken Object Level Authorization) or IDOR can lead to sensitive data exposure and unauthorized operations.
Excessive User Permissions
Granting users more permissions than necessary increases the risk of accidental or malicious misuse. Limiting roles to the principle of least privilege ensures safer, more controlled API access.
Privilege Escalation Risks
Flaws in role management or access policies can let attackers elevate their privileges. Careful monitoring and strict enforcement of access rules prevent users from gaining unauthorized capabilities.
API Endpoints with Missing Access Checks
Endpoints without proper access verification are easy entry points for attackers. Consistently applying authorization checks across all API routes strengthens authorization security and protects critical data.
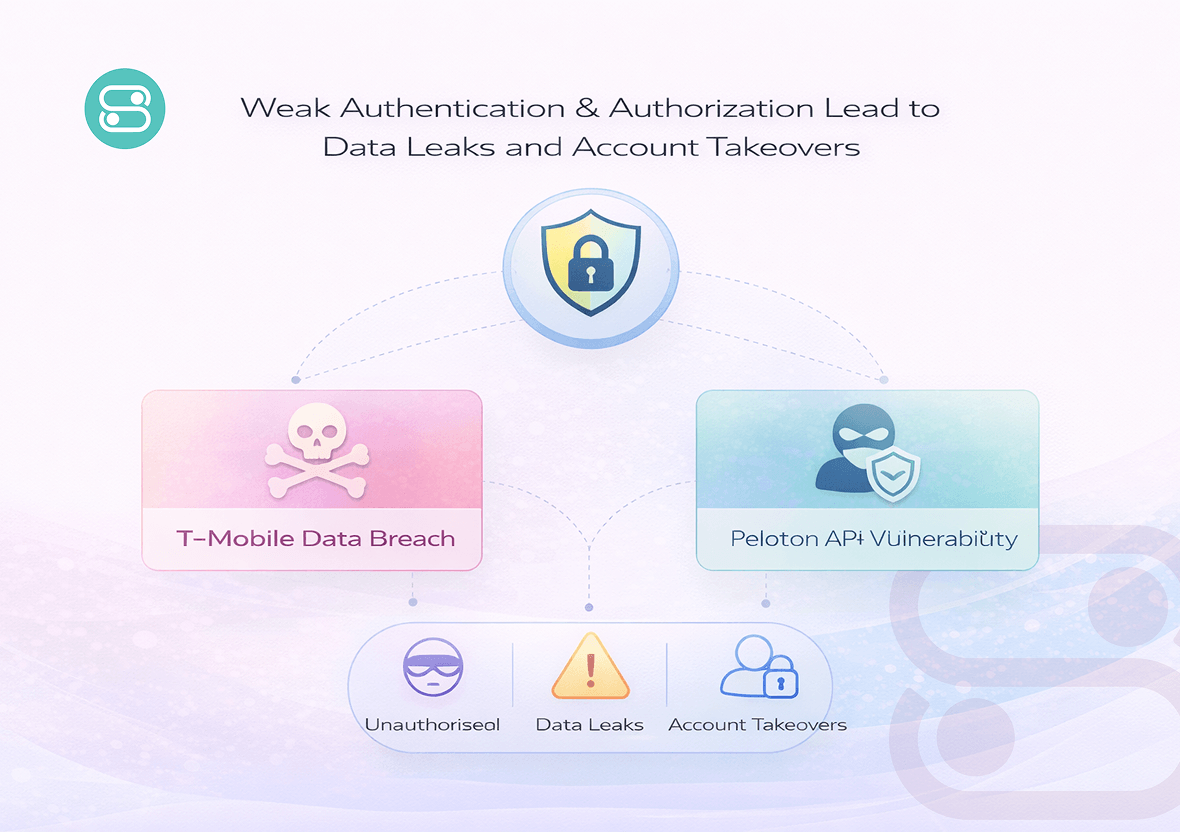
How Authentication & Authorization Vulnerabilities Are Exploited
Authentication and authorization flaws in APIs are not just theoretical risks. They get exploited in the real world with serious impact.
When an API lacks strong checks to verify identities or control access, attackers can gain unauthorized API access, extract sensitive data, and even take over accounts which appear legitimate to the system.
A clear example occurred with T‑Mobile in 2023, when attackers exploited insufficient authorization controls in an API to harvest personal information of millions of customers. Similarly, researchers found that Peloton’s API endpoints failed to validate user permissions correctly, allowing access to private user data simply by misusing query parameters.
These incidents show how weak authentication and access control mechanisms can lead directly to data leaks, unauthorized access, and account takeovers, underlining the need for robust security practices at every API boundary.
Our Solution Overview
Securing APIs requires an extensive approach which addresses both authentication and authorization vulnerabilities in real time. Our solution consistently monitors API requests to enforce identity verification and ensures only authorized users can access sensitive endpoints.
By combining api authentication with strict access control enforcement, we prevent unauthorized API access and reduce the risk of data leaks. Additionally, the platform supports multi factor authentication implementation to strengthen verification for all users, making it harder for attackers to bypass security controls.
This layered approach ensures that APIs remain reliable, compliant, and resistant to common attack vectors, while simplifying management for development and security teams.
- Real time api authentication monitoring for all requests
- Enforcement of role based and object level access controls
- Support for multi factor authentication across endpoints
- Detection and blocking of suspicious or malformed requests
- Comprehensive logging for compliance and auditing purposes
Advanced Authentication Security Features for APIs
Two Factor Authentication
Adds an extra layer of security by requiring a second verification step beyond the password. Integrating two factor authentication reduces the risk of unauthorized API access even if credentials are compromised.
Multi-Factor Authentication
Combines multiple verification methods like OTPs, biometrics, or hardware tokens. Using multi factor authentication strengthens overall authentication security and prevents account takeover.
Passwordless Authentication
Eliminates reliance on passwords by using secure tokens or device based verification. This reduces password related vulnerabilities while maintaining smooth access for authorized users.
API Token Management
Ensures tokens are issued, rotated, and revoked securely to control API access. Proper token lifecycle management protects sensitive endpoints from misuse or unauthorized calls.
Risk-Based Authentication
Adapts security requirements based on user behavior, device, or location. Dynamic checks help prevent suspicious activity without disrupting legitimate API interactions.
Modern Authorization Mechanisms to Secure API Endpoints

Role Based Access Control (RBAC)
Assigns permissions based on user roles to ensure users can only access what they are authorized for. Implementing authorization security through RBAC minimizes the risk of privilege abuse and data exposure.

Object-Level Access Checks
Validates access to individual resources or data objects within APIs. This granular control prevents unauthorized operations and ensures sensitive data remains protected.

Privilege Auditing
Tracks and reviews user permissions and access patterns over time. Regular auditing helps identify excessive privileges and potential security gaps before they are exploited.

API Endpoint Access Monitoring
Continuously monitors API calls to detect abnormal or unauthorized access attempts. Real-time monitoring reinforces api authentication security and ensures policies are consistently enforced across all endpoints.
Benefits of Using Our Service
- Enforces strict api authentication security to block unauthorized access, ensuring that only verified users can interact with sensitive API endpoints.
- Provides granular authorization security controls, allowing precise management of which users can access specific resources and perform particular actions.
- Ensures regulatory compliance with GDPR, HIPAA, and SOX by generating detailed logs, audit-ready records, and continuous monitoring of all API activity.
- Monitors API interactions in real time, detecting both internal misuse and external attacks, keeping sensitive data and operations protected at all times.
- Automates enforcement of authentication and authorization rules, reducing human errors, operational gaps, and the risk of security oversights.
- Strengthens overall API reliability, maintains data integrity, and builds user and client trust by ensuring consistent, secure access across all endpoints.

Industries That Need Authentication & Authorization Security
Finance & Banking
Protect transaction APIs from unauthorized access and fraud attempts. Strong api authentication security ensures only verified users can execute financial operations safely.
E-commerce
Prevent order errors, account takeovers, and API abuse that can disrupt customer transactions. Granular authentication and access control maintain trust and reliability across online platforms.
Technology / SaaS
Protect SaaS APIs from unauthorized usage and data leaks in multi-tenant environments. Combining robust api authentication security with strict authorization policies ensures safe and scalable operations for tech products.
Advanced Validation Features for Modern APIs
Financial Services API Protection
Problem:
A banking client experienced frequent unauthorized API access attempts, leading to transaction failures and compliance concerns.
Solution:
We implemented strong api authentication security with token validation and role‑based access controls across all financial endpoints.
Result:
Unauthorized access attempts dropped by 95% with zero compliance violations reported in six months.
Healthcare Data Integrity
Problem:
A healthcare provider struggled with unauthorized read access to patient records via unsecured APIs.
Solution:
We deployed layered authentication and access checks, enforcing stringent authorization rules on every data request.
Result:
Data leakage incidents were reduced to 0, and audit readiness scores increased by 43% within the first quarter.
E‑commerce Abuse Mitigation
Problem:
An online retailer faced account takeovers and order manipulation due to weak access controls.
Solution:
We integrated multi‑factor authentication and continuous access monitoring into critical API workflows.
Result:
Account takeover incidents decreased by 88% and verified order accuracy improved by 32%
Secure API Access with Policy-Driven Controls
Apply granular api authorization rules and authentication mechanisms across your API ecosystem. Maintain strict control over who can access what- without impacting performance.
Frequently Asked Questions
Authentication verifies who the user or system is. Authorization determines what they are allowed to access. Together, they form the foundation of api authentication and api authorization.
Adding layers like two factor authentication, multi factor authentication, and passwordless authentication reduces reliance on passwords and blocks unauthorized access even if credentials are compromised.
Implement strong authentication security practices, enforce strict access controls, and continuously monitor API activity to detect and prevent misuse early.
Yes. The solution is designed to support modern architectures, ensuring consistent api authentication security across both REST and GraphQL APIs.


