Phishing Protection for Enterprises
Phishing Protection for Enterprises
Stop Phishing from Becoming an Identity Breach. Protect Identities Beyond the Inbox.
SecurEnds gives security teams clear visibility into which users and privileges are exposed. It monitors identity behavior and stops attackers from moving laterally. By linking phishing activity directly to identity risk, SecurEnds helps enterprises reduce potential breaches before they escalate.
- Identify and contain compromised accounts in real time
- Monitor privileged access and risky credentials automatically
- Prioritize response based on actual identity exposure, not just the email
Phishing Is No Longer an Email Problem – It’s an Identity Crisis
Phishing attacks have evolved far beyond the inbox. Modern attackers target identity and access, using stolen credentials and compromised OAuth tokens to move laterally across enterprise systems.
Even when emails are delivered safely, valid accounts can be hijacked and privileges will be misused resulting in exposure of sensitive applications. The risk is not just the message itself. It is what happens after the click.
Without visibility into identity exposure, organizations face invisible threats which are capable of causing serious operational and compliance damage.
Modern Phishing Attacks Target Identity, Not Just Email
Credential Harvesting
Attackers create fake login pages to trick users into revealing usernames, passwords, or session tokens. This gives them direct access to enterprise accounts.
MFA Fatigue & Push Bombing
Repeated authentication prompts pressure users into approving malicious sign-ins. Attackers exploit this to bypass multi-factor protections.
OAuth & Token Based Phishing
Malicious apps request OAuth permissions, allowing attackers persistent access to data without needing credentials. Tokens can be silently abused across services.
Business Email Compromise
Attackers create fake login pages to trick users into revealing usernames, passwords, or session tokens. This gives them direct access to enterprise accounts.
Internal Lateral Phishing
Compromised accounts are used to send phishing emails internally, leveraging trust between employees to spread attacks further within the organization.
Targeted Social Engineering
Sophisticated campaigns manipulate users with context specific messaging, exploiting knowledge of roles, responsibilities, and internal processes.
The real threat is not the email. It is what attackers can do once they control access.
Why Legacy Phishing Protection Falls Short
Security is only effective when identity exposure and risk are visible. True protection requires monitoring identities, privileges, and access, not just messages.
Without identity context, attacks go undetected.
Why Partner with Us as Your API Security Company?
Detect
Consistently monitor accounts, credentials, and authentication activity for phishing indicators.
Correlate
Link suspicious behavior to roles, privileges, and access paths to understand exposure.
Prevent
Automatically block misuse of compromised accounts and sensitive privileges.
Remediate
Revoke risky access, reset affected sessions, and reduce overall identity risk.
Works with your existing email, IAM, and IGA systems to contain identity threats post phish.
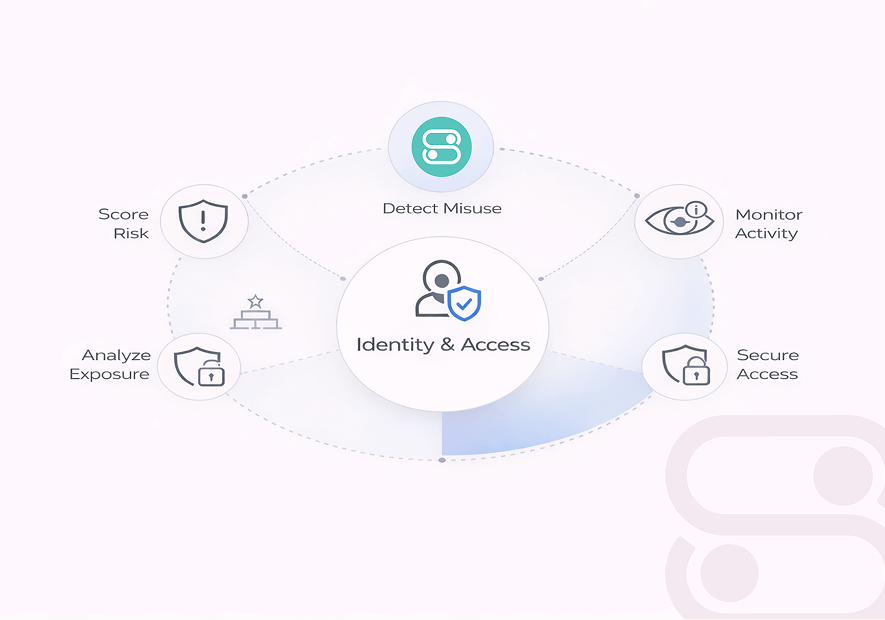
Identity Aware Phishing Detection
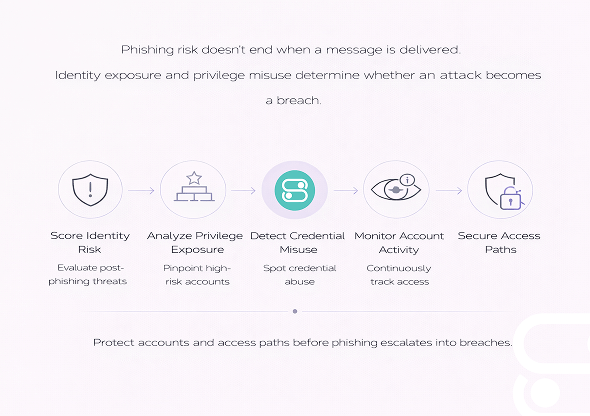
SecurEnds approaches phishing protection differently by focusing on the identity layer, not just the inbox. While traditional tools stop at scanning messages, SecurEnds consistently evaluates the impact of phishing on user accounts and privileges.
By analyzing which identities are exposed and how privileges could be abused, security teams gain real time insight into risk. This will reduce possible breaches even after phishing emails bypass email gateways.
Key capabilities :
- Identity risk scoring for users and accounts after phishing events
- Privilege exposure analysis to highlight sensitive roles and access paths
- Detection of credential and OAuth token misuse
- Consistent monitoring of account activity for abnormal access patterns
Protect accounts and access paths before phishing escalates into breaches.
What Happens After a Phishing Attempt Matters Most
Detecting phishing is just the beginning. The real risk comes from which accounts and systems are exposed once an attacker succeeds. SecurEnds provides continuous post phish visibility, mapping compromised identities to their access rights and sensitive applications.
Security teams can prioritize action based on actual exposure, not generic alerts. This let them take steps to prevent lateral movement and minimize breach impact.
By focusing on identity risk and access context, SecurEnds ensures post phish response is precise and effective.
Contain Exposed Identities
Lock compromised accounts immediately.
Secure At-Risk Access
Revoke risky sessions, reset credentials, and review privilege assignments.
Prioritize Remediation
Address highest risk accounts and critical systems first to limit damage.
Built for Compliance and Audit Readiness
Meeting regulatory standards requires documenting actions and proving proactive risk management. SecurEnds helps enterprises align with regulatory expectations by providing audit ready reporting and consistent tracking of identity and access changes.
Security teams can demonstrate compliance and review account activity across all critical systems. With automated logs and structured reports, organizations can respond confidently to audits while maintaining robust identity focused phishing defenses.
Compliance alignment
Audit-ready reports
Access change tracking
Proof of proactive risk mitigation
What Security Teams Say

Meera Kapoor,
Security ArchitectWe used to scramble after phishing incidents. Now, SecurEnds helps us stay ahead, and the team actually enjoys using it.

Rohan Shetty,
Cloud Security ManagerIt is not just about blocking emails. It is knowing our identities are protected. That peace of mind is priceless.
Trusted by Security and Compliance Teams
Built for identity-first, regulated enterprises. Enterprises across industries rely on SecurEnds to protect identities and simplify compliance. Our solutions give security teams clear visibility and audit ready reporting to prevent breaches before they escalate.
Why Enterprises Choose Securends
Trusted by regulated organizations worldwide, SecurEnds delivers solutions which go beyond traditional email defenses to protect accounts and access across complex environments.
Identity First Security Architecture
Built to secure users and privileges, not just email messages.
Identity First Security Architecture
Enforces consistent verification and limits implicit trust across all identities.
Cloud and SaaS Native
Smoothly integrates with Microsoft 365, Gmail, and other cloud platforms without disrupting workflows.
Built for IAM and IGA Teams
Designed to give identity and access teams actionable visibility and control.
Enterprises select SecurEnds because it combines deep identity security expertise with proven, enterprise ready technology.
Frequently Asked Questions
Email security stops malicious messages. SecurEnds focuses on what happens after phishing. It will track identity exposure and misuse of valid credentials.
No. It works alongside secure email gateways. It will add identity aware visibility and control after phishing bypasses inbox defenses.
Yes. It detects MFA fatigue and abnormal authentication behavior traditional MFA controls often miss.
Absolutely. SecurEnds monitors compromised identities and evaluates exposed access to prevent further misuse even after a click occurs.
Deployment is API based and typically completed quickly with no agents and heavy infrastructure changes.
Yes. SecurEnds integrates with IAM, IGA, and cloud identity platforms to correlate phishing signals with roles and access paths.
Stop Phishing Attacks Before They Turn Into Identity Breaches
Phishing is inevitable. Gain visibility into exposed identities, risky access, and post phish activity and respond before attackers move deeper into your environment.


