Identity First Account Takeover Detection
Identity First Account Takeover Detection
Stop unauthorized access to high value accounts and prevent privilege misuse before attackers can escalate.
SecurEnds protects enterprises from account takeover attempts targeting high value identities. By correlating login activity and identity context, SecurEnds helps security teams detect and remediate threats in real time. The platform strengthens governance across cloud and hybrid environments.
- Identify suspicious account behavior before it escalates.
- Prioritize high risk users and sensitive access paths.
- Block unauthorized access and prevent lateral movement.

Modern Account Takeover Threats Require Identity Aware Protection
Modern attackers exploit credentials and OAuth token misuse to impersonate privileged accounts. If an account is compromised, attackers can move laterally. They can escalate privileges and exfiltrate sensitive data without raising alerts.
Traditional security tools often fail to detect these identity focused attacks. Enterprises lose visibility over which accounts are exposed and which access is at risk. For regulated organizations, these breaches can also result in compliance violations and reputational damage.
Security teams need a solution which connects account activity to identity context and risk impact enabling proactive detection and rapid containment.
The Evolving Threat Landscape of Account Takeovers
Credential Theft & Reuse
Attackers use stolen or leaked passwords across multiple systems to gain access. Reused credentials on privileged accounts can lead to rapid compromise.
MFA Fatigue & Bypass
Repeated authentication prompts or exploitation of weak MFA flows force user approval, allowing unauthorized access without password theft.
OAuth Token Abuse
Malicious apps or compromised token consent grant attackers persistent access to enterprise resources and SaaS applications.
Session Hijacking & Lateral Movement
Compromised sessions allow attackers to move laterally across internal systems. They will escalate privileges and access sensitive workflows.
Insider Impersonation
Threat actors utilize trusted accounts internally or via social engineering to bypass detection and exfiltrate data.
Targeted Executive & Privileged Account Attacks
High value accounts are specifically targeted to manipulate approvals, financial transactions, or access to critical systems.
Security teams need visibility into identity context and access privileges to protect from account takeover attacks.
Traditional Detection Fails Against Identity Focused Attacks
Legacy security tools focus on logins and alerts but fail to detect risk across identities and privileges. Consistent identity aware monitoring is essential to stop account takeover before it escalates.
Traditional tools stop at the login – attackers exploit privileges and trust beyond that.
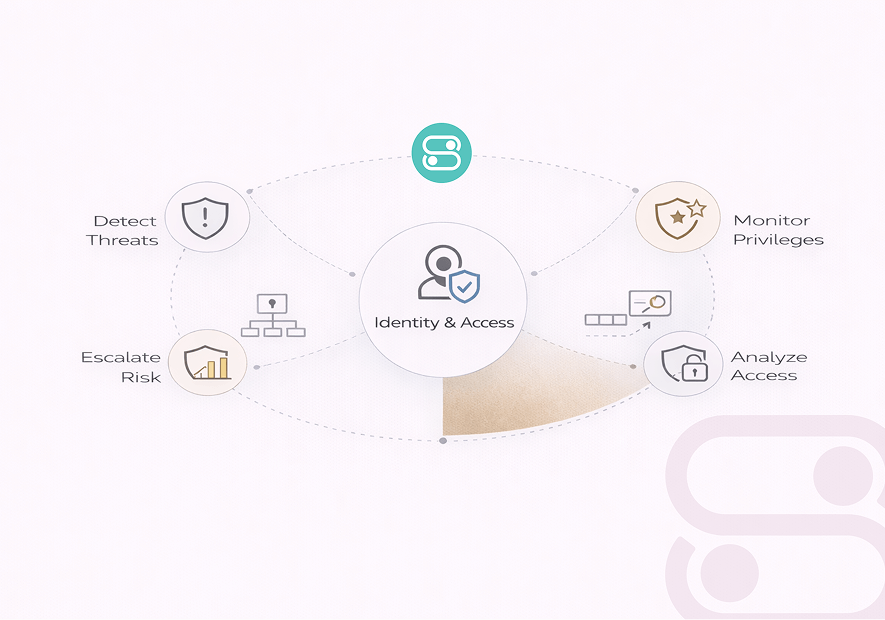
Account Takeover Detection in Action
Detect
Monitor logins, privilege changes, and unusual activity across high value accounts in real time.
Correlate
Connect account behavior to identity context, roles, and access privileges to understand risk.
Prevent
Block suspicious logins, disable compromised sessions, and stop lateral movement before escalation.
Remediate
Automate credential resets and account lockdown to reduce exposure quickly.
By linking identity, access and behavior, SecurEnds ensures attackers are blocked before they can escalate privileges.
Prevent Takeovers Beyond Credentials
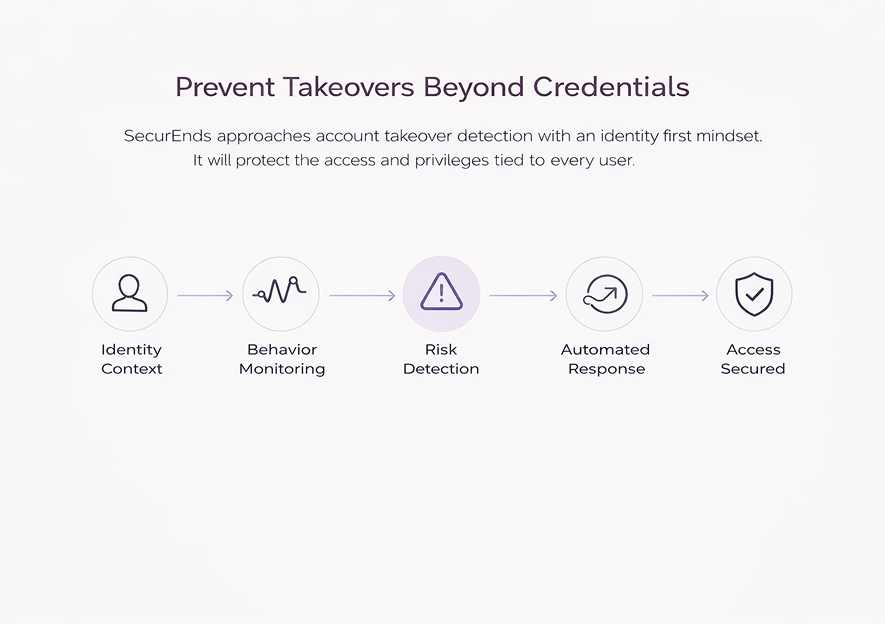
SecurEnds approaches account takeover detection with an identity first mindset. It will protect the access and privileges tied to every user. By prioritizing identity context and access exposure, the platform detects and prevents compromise before it escalates.
Automated remediation reduces response time and ensures consistent governance. Enterprises gain visibility into risky accounts and possible lateral movement across the organization.
- Consistent monitoring of high value and privileged accounts
- Real time detection of anomalous logins and behavioral changes
- Risk based prioritization for immediate response
- Automated credential resets and privilege adjustments
Identity first detection ensures attackers are blocked and enterprise access remains under control.
What Happens After an Account Takeover Attempt
Detecting a potential account takeover is only the first step. Understanding the resulting exposure is what protects your enterprise. SecurEnds provides clear visibility into which accounts were targeted and any downstream systems that could be affected.
Security teams can immediately prioritize response based on account criticality and exposure. This will reduce the chances of lateral movement or privilege escalation.
By correlating identity behavior with risk context, enterprises will gain valuable insights. This empowers teams to act decisively and maintain compliance while minimizing operational disruption.
Identify Accounts
See exactly which users were targeted.
Assess Risk
Understand what access could be compromised.
Prioritize Action
Focus on high risk accounts first.
Stay Audit Ready While Preventing Takeovers
Account takeover attacks can create regulatory and audit risks if high value accounts are compromised without detection. SecurEnds helps enterprises maintain compliance by tracking account activity and remediation actions in a fully auditable way.
Security and compliance teams can demonstrate regular monitoring, access control, and threat mitigation while reducing audit findings and governance gaps.
Compliance alignment
Audit-ready reports
Access change tracking
Proof of proactive risk mitigation
What Teams Say About SecurEnds

Priya Nair,
Cloud Security ArchitectSecurEnds fits smoothly into our IAM stack. We finally feel in control of privileged accounts and high value users.

Rhea Malhotra,
IAM LeadWorking with SecurEnds has made our account security far more manageable. We now spot risky logins instantly and act before they escalate.
Trusted Across Industries
From large scale cloud deployments to hybrid environments, our platform helps security and compliance teams reduce identity risk. Built for regulated, identity first enterprises, SecurEnds ensures every account takeover attempt is detected and remediated effectively.
Why Enterprises Choose SecurEnds
When identities are the new perimeter, visibility and control matters a lot. SecurEnds helps enterprises stay ahead of account takeover risk with confidence.
Identity First Security Architecture
SecurEnds is built around identities, ensuring account takeover risks are analyzed in full context.
Aligned with IAM and IGA Teams
The platform works alongside IAM and IGA systems, extending visibility without disrupting existing workflows.
Zero Trust Aligned by Design
Every access event is continuously evaluated, assuming breach and validating trust in real time.
Cloud and SaaS Native
SecurEnds integrates smoothly across cloud, SaaS, and hybrid environments without heavy operational overhead.
SecurEnds doesn’t just detect account takeovers. It gives teams the clarity to stop them early. This is why enterprises trust it as part of their identity security foundation.
Frequently Asked Questions
It monitors unusual login behavior, privilege changes, and anomalous activity patterns across user accounts in real time.
Yes. By correlating account behavior with role privileges, SecurEnds can block unauthorized access and prevent lateral movement.
Absolutely. The platform protects accounts across cloud services, SaaS apps, and hybrid environments without requiring heavy custom configuration.
Threats are flagged instantly based on identity risk and access context, allowing teams to act within minutes.
Yes. It complements IAM, IGA, and SIEM tools for automated detection, response, and audit ready reporting.
SecurEnds logs account exposure, access changes, and remediation actions to meet SOC 2, ISO, SOX, and GDPR standards.
Take Control of Identity Risk Before It Becomes a Breach
Protect your enterprise accounts from takeover with real time detection and identity aware response.


