Hybrid Banking Identity Blind Spots
Hybrid Banking Is Creating Identity Blind Spots.
Banks did not gradually move to hybrid environments — they accelerated into them. Cloud adoption expanded rapidly, digital channels multiplied, and collaboration platforms became essential. At the same time, core banking systems remained foundational and mission-critical. The result is a modern financial institution operating across on-premises infrastructure, cloud identity platforms, SaaS applications, and legacy core systems.
The problem is not the technology shift. It is that identity governance did not evolve at the same speed. Today, users exist simultaneously across Microsoft Active Directory, Microsoft Entra ID, and Microsoft 365, while also maintaining access inside core banking platforms such as SilverLake. Each of these systems manages roles, permissions, and entitlements differently. Each has its own administrative model. Each produces its own access data.
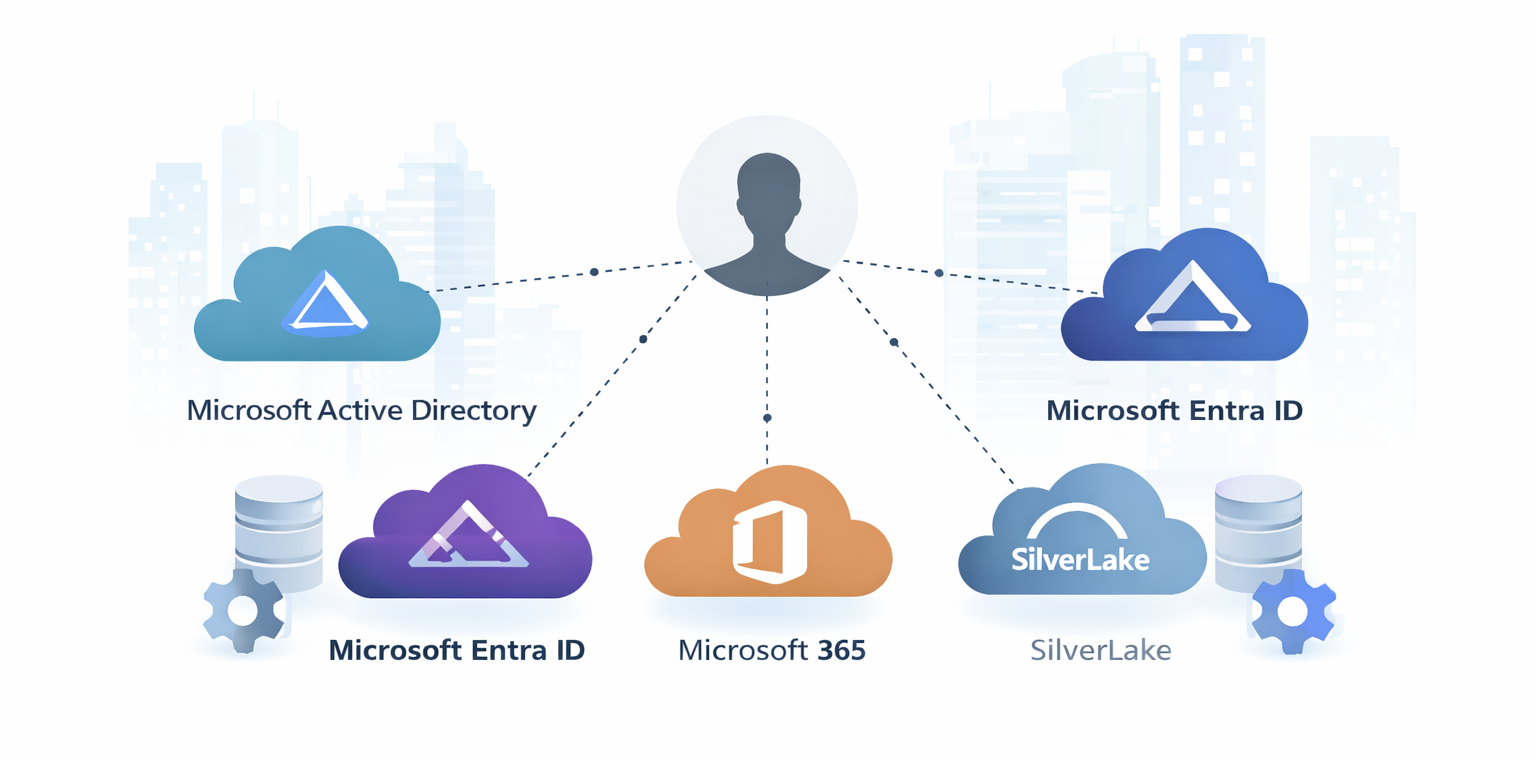
What most institutions lack is unified visibility across all of them.In a hybrid bank, a single employee might be:
A member of multiple Active Directory security groups
Assigned privileged roles in Microsoft Entra ID
Granted access to sensitive SharePoint or Teams environments in Microsoft 365
Designated as a security officer in JackHenry SilverLake
Authorized for wire initiation or approval through IS9145P settings
When access governance is managed in silos, these entitlements are reviewed independently — if they are reviewed at all. Security teams often export reports, manipulate spreadsheets, and route approval emails manually. Core banking access may be reviewed quarterly, while cloud permissions are reviewed on a different cadence. Some systems may rely on static role attestations with limited validation.
Over time, this fragmentation creates identity blind spots.Privileged access can accumulate unnoticed. Terminated or transferred employees may retain residual permissions across cloud or core systems. Wire authority and administrative roles may not be reconciled against separation-of-duty policies. Audit evidence becomes a reactive exercise, requiring teams to compile proof from multiple disconnected data sources. Regulators increasingly expect defensible governance over access to financial systems, especially where high-risk functions like security administration or wire transfers are involved. Yet without centralized visibility, institutions struggle to confidently answer a simple question: Who has access to what, and why?
Forward-looking institutions are shifting their perspective. Instead of treating identity as a byproduct of infrastructure, they treat it as the control plane of the enterprise. Centralized identity governance aggregates access data from across environments — on-premises directories, cloud identity providers, collaboration platforms, and core banking systems. For institutions running SilverLake, that includes ingesting security extracts such as IS9143P (User ID Profile Settings), IS9141P (Security Officer Access), and IS9145P (Wire Settings) directly in their native format.
SecurEnds enables institutions to unify this access data without requiring manual transformation or reformatting. Reports exported from SilverLake are ingested as generated. Active Directory, Microsoft Entra ID, and Microsoft 365 entitlements are connected through automated integrations. The platform normalizes the data internally, presenting reviewers with contextualized, actionable access information.Traditional access reviews are often quarterly exercises driven by compliance deadlines. They are time-bound, labor-intensive, and prone to delays. A centralized governance model shifts the paradigm from periodic review to continuous oversight.
Automated certification campaigns can be scheduled for recurring review cycles. High-risk access — such as security officer privileges or wire permissions — can be reviewed more frequently. Managers and application owners receive structured review workflows with built-in reminders and escalation paths. Every approval or revocation decision is timestamped and documented automatically. Audit evidence is no longer assembled retroactively. It is generated as part of the governance process itself. This shift reduces operational burden while strengthening internal controls. More importantly, it enables institutions to enforce least-privilege access consistently across both cloud and core systems.
Hybrid banking environments are here to stay. Cloud adoption will continue to expand, while core systems remain critical to daily operations. Complexity is not the enemy — unmanaged identity complexity is. Institutions that unify access governance across Active Directory, Microsoft Entra ID, Microsoft 365, SilverLake, and other critical applications eliminate blind spots that expose them to regulatory, operational, and fraud risk. By centralizing identity visibility and automating access certifications, banks move from reactive audit preparation to proactive risk management. Governance becomes embedded in daily operations rather than triggered by compliance events. In a hybrid world, identity is the connective tissue across every system. When institutions treat it as such, they regain control, strengthen compliance posture, and create a defensible, scalable foundation for growth.
Hybrid complexity does not have to mean governance uncertainty. With the right approach, it becomes manageable — and measurable.


