Financial Fraud Detection for Modern, Cloud First Enterprises
Financial Fraud Detection for Modern, Cloud First Enterprises
Move beyond rule based fraud controls with identity aware risk detection.
SecurEnds enables financial fraud detection by consistently analyzing identity behavior and risk signals. By connecting identity context with financial activity, SecurEnds helps security and IAM teams detect fraud earlier. It will reduce business impact without disrupting legitimate operations.
- Detect identity driven financial fraud across applications and systems
- Identify risky access, privilege abuse, and anomalous activity early
- Reduce fraud impact with contextual, risk based response actions
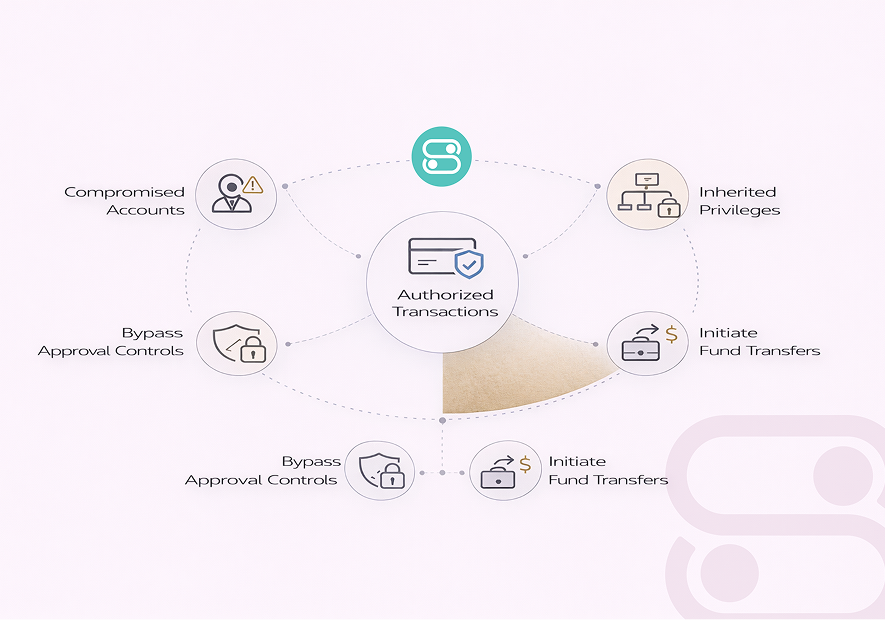
The Hidden Risk Behind Authorized Financial Actions
Modern financial fraud rarely starts with a single suspicious transaction. It begins with compromised user accounts and inherited privileges. It could be stale access in finance systems or abused service identities tied to payment workflows.
Attackers exploit valid credentials and application level access to initiate fund transfers and bypass approval controls. Transaction focused tools lack visibility into who initiated an action and what access enabled it. This gap leaves enterprises blind to fraud which operates entirely within legitimate systems and workflows.
Without identity aware fraud detection, risky financial actions are discovered late, often during reconciliation or after financial loss has already occurred.
Common Identity Driven Financial Risks
Privilege Escalation
Attackers abuse over provisioned access or stale roles to execute financial transactions they shouldn’t have permission for.
Unauthorized Payments
Compromised accounts initiate fund transfers or manipulate payment workflows without triggering alerts.
Vendor & Payroll Manipulation
Fraudsters alter vendor bank details and add phantom vendors. They will adjust payroll settings to divert funds.
API / Integration Abuse
Malicious or compromised tokens in connected apps can automate fraudulent transactions and bypass approval workflows.
Service Account Misuse
Exploiting unattended service identities or system accounts to carry out financial actions undetected.
Internal Collusion
Employees or contractors intentionally misuse legitimate access to commit financial fraud. This is often hard to spot.
Enterprise fraud hides in plain sight, within trusted accounts and routine workflows.
The Blind Spots of Legacy Financial Controls
Static rules catch the easy cases but modern fraud hides in legitimate workflows. Without identity aware controls, high impact financial fraud goes undetected until it is too late.
Fraud detection that ignores identity is blind to the real attack path.
How Fraud Detection Works Across Access and Finance Systems
Detect
SecurEnds consistently monitors user accounts and system activity for anomalies indicating possible financial fraud. Behavioral patterns and privilege use are analyzed in real time to flag risks early.
Correlate
Signals are mapped to roles and privileges across financial systems and SaaS platforms. This contextual view ensures alerts focus on actual risk, not noise.
Prevent
Compromised identities are automatically restricted and monitored to stop fraudulent transactions before they occur. Policy driven enforcement minimizes disruption to legitimate business operations.
Remediate
Access revocations and risk mitigation workflows are automated for rapid response. Teams gain audit ready trails of actions for compliance and governance.
Identity aware protection ensures risky access is detected, acted on, and audited in real time.
Stopping Fraud at the Source, Not Just the Transaction
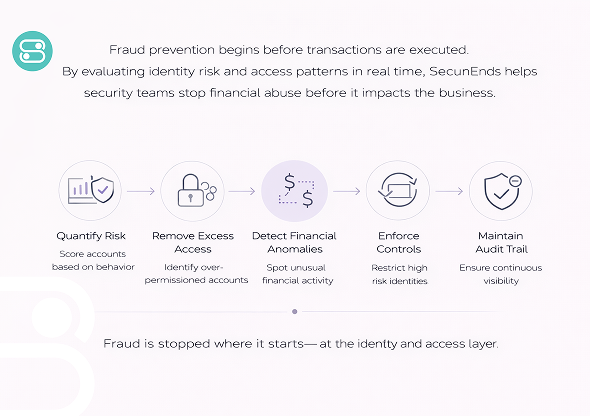
SecurEnds protects enterprises from financial fraud by combining identity intelligence with transaction context. Instead of relying on static rules or post transaction alerts, it evaluates risk at the user and privilege level.
Our approach identifies suspicious behavior across ERP and payment systems before losses occur. By correlating identity signals with business critical actions, SecurEnds provides valuable insights for security teams.
Key Capabilities
- Quantifies risk based on user behavior and access.
- Detects over permissioned or stale accounts.
- Flags unusual financial workflows and API activity.
- Restricts high risk identities and maintains audit trails.
SecurEnds stops fraud where it begins, at the identity and access layer.
Gain Full Control After a Financial Risk Event
Detecting a financial fraud attempt is only the first step. The critical value lies in understanding which identities and accounts are exposed and which financial actions could be impacted.
SecurEnds provides post incident visibility to map risky activity across ERP systems and payment workflows. By correlating access, privilege, and transaction patterns, security teams can prioritize responses based on actual business impact rather than generic alerts.
This operational insight ensures compromised accounts are quickly isolated and suspicious transactions are halted. So auditors will have clear evidence of proactive mitigation.
Post incident visibility also strengthens enterprise governance by showing which workflows or APIs contributed to the risk. This will empower teams to harden controls and prevent repeat incidents.
Isolate Compromised Identities
Block high risk accounts immediately.
Prioritize Critical Transactions
Focus on sensitive workflows first.
Audit and Report
Generate compliance ready logs.
Aligning Financial Fraud Detection with Regulations
Financial institutions face strict regulatory obligations, and any fraud incident can have serious legal and financial repercussions. SecurEnds ensures compliance alignment by integrating identity aware fraud detection with audit and governance workflows.
Compliance alignment
Audit-ready reports
Access change tracking
Proof of proactive risk mitigation
Hear from Security and Finance Professionals

Arjun Patel,
Senior Security AnalystThe team’s approach is practical and fast. We can now track high risk accounts without drowning in alerts.

Nora Singh,
Compliance ManagerSecurEnds gave us visibility we didn’t have before. Our compliance reporting is cleaner, and the finance operations team trusts the system completely.
Built for Regulated Industries
SecurEnds is trusted by banks, fintech companies, and global enterprises to protect against financial fraud. Our platform is designed for highly regulated industries, providing visibility and compliance ready reporting. Organizations rely on SecurEnds to secure sensitive transactions and reduce exposure, all while keeping auditing and governance simple and effective.
Why Enterprises Partner With Securends
SecurEnds delivers identity aware fraud protection designed for enterprise scale operations
Identity First Architecture
Maps every transaction and account activity to real user identities, revealing hidden fraud risks in real time.
Zero Trust Enforcement
Consistently validates every action and transaction, preventing unauthorized access or escalation within financial systems.
Cloud & SaaS Native
Smoothly protects ERP, banking, and payment platforms without disrupting workflows or user experience.
Built for IAM & IGA Teams
Enables teams to monitor privileges, enforce policies, and remediate high risk accounts quickly and confidently.
SecurEnds gives enterprises full visibility and control to prevent financial fraud at scale.
Frequently Asked Questions
SecurEnds helps detect fraud tied to compromised identities and unauthorized financial actions across users and systems.
Most tools focus on transactions. SecurEnds focuses on who is performing the action and their access level.
Yes. SecurEnds identifies risky behavior and abnormal access patterns. It will also detect misuse of legitimate credentials after compromise.
Absolutely. SecurEnds works alongside IAM, IGA, SIEM, and financial platforms without replacing existing controls.
By correlating identity risk with access and activity, teams can act early and maintain audit ready controls.
Yes. SecurEnds is built for complex, high volume environments where financial risk and compliance intersect.
Detect Financial Fraud Where Access Meets Action
When identities are misused, financial controls fail silently. SecurEnds brings identity context into fraud detection so teams can stop misuse and stay audit ready.


