fda-21-cfr-part-11-automated-user-access-entitlement-reviews
FDA 21 CFR Part 11 Automated User Access &
Entitlement Reviews
CHALLENGE:
In accordance with 21 CFR Part 11 there are a range of features that organizations are required to have in place when implementing a computer system to manage electronic records and processes. Assurances for audit trail functionality, electronic signatures, security and data integrity, records retention and file formats are to name but a few. Periodic user access reviews will help to identify accounts that have been assigned excessive privileges, accounts with access that have not been updated to reflect job position changes, and dormant accounts. Failing to perform user access reviews on a regular basis will place the organization n at a higher risk for:
- A terminated employee gaining remote access to the network or email systemt
- Misuse of dormant administrative accounts
- Segregation of duties issues if an employee moves to a new department, but retains system privileges from the previous department
SOLUTION:
SecurEnds helps comply with Part 11 to limit user access and their privileges by automating the certification process for organization
- Faster review and perform access certification
- Proof of compliance for auditors
- Reduce insider threat by removing unneeded access privileges
- Replace manual processes with automated reporting and approval workflows
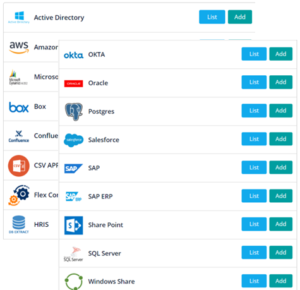
Step 1: Connect Applications
Manage the discovery of identities across connected and disconnected applications across the IT landscape. Match identities to the system of record. Use CSV upload, Pre-build Connectors, FlexConnectors, and Service Desk integration. Integrates with ITSM system(ServiceNow, JIRA, etc) to update the changes.
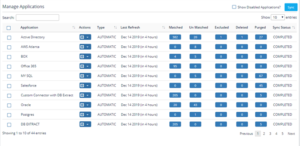
Step 2: Discover Identities
Centralize access controls and consolidate identity repositories. Powered by artificial intelligence and machine learning, Discovery Module enables auto-discovery of identities, including orphaned and unauthorized accounts.
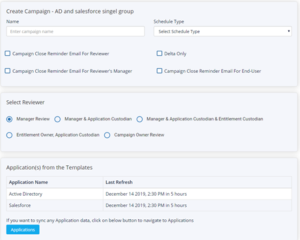
Step 3: Intelligent Campaigns
Schedule automated access review campaigns by multiple dimensions (roles etc). Call to action intelligent reminders for end-users, approvers and skip level approvers. “Delta Campaign”, a quick snap campaign, allows you to see the changes since the last review.
Step 4: Reports & Insights
Our AI/ML module presents a simplified analytics workflow for outliers based on their risk profiles and excessive privileges. Drill down by campaigns, applications and periods.

FEATURES:
- Access Certification : automate inadequate and/or time-consuming manual access certification, user attestations etc to meet security compliance and internal IT control requirements
- Audit Evidence : demonstrate compliance with standards and provide proof-of-compliance using pre-defined audit reports, audit trail mechanisms and certification of access
- Segregation of duty (SOD) create rules that prevent risky sets of access from being granted to a person. For example, the ability to both view a bank account and transfer funds to outside accounts
- Analytics & Reporting: use AI/ML driven reports to identify risk outliers, generate drill down reports to identify risky entitlements
- Automate Provisioning and De-provisioning: streamline the review and verification (or revocation) of users access to different apps and resources.
- Increase Security Posture : comprehensive identity governance solution that reduces identity security risk and insider threat by eliminating orphaned and unauthorized user accounts
- Centralize Visibility : Track access of all users (including contractors and partners) who join, move or leave the company


