Access Review Template for Compliance: Components, Best Practices & Free Download
Access Review Template for Compliance: Components, Best Practices & Free Download

Why You Need a User Access Review Template
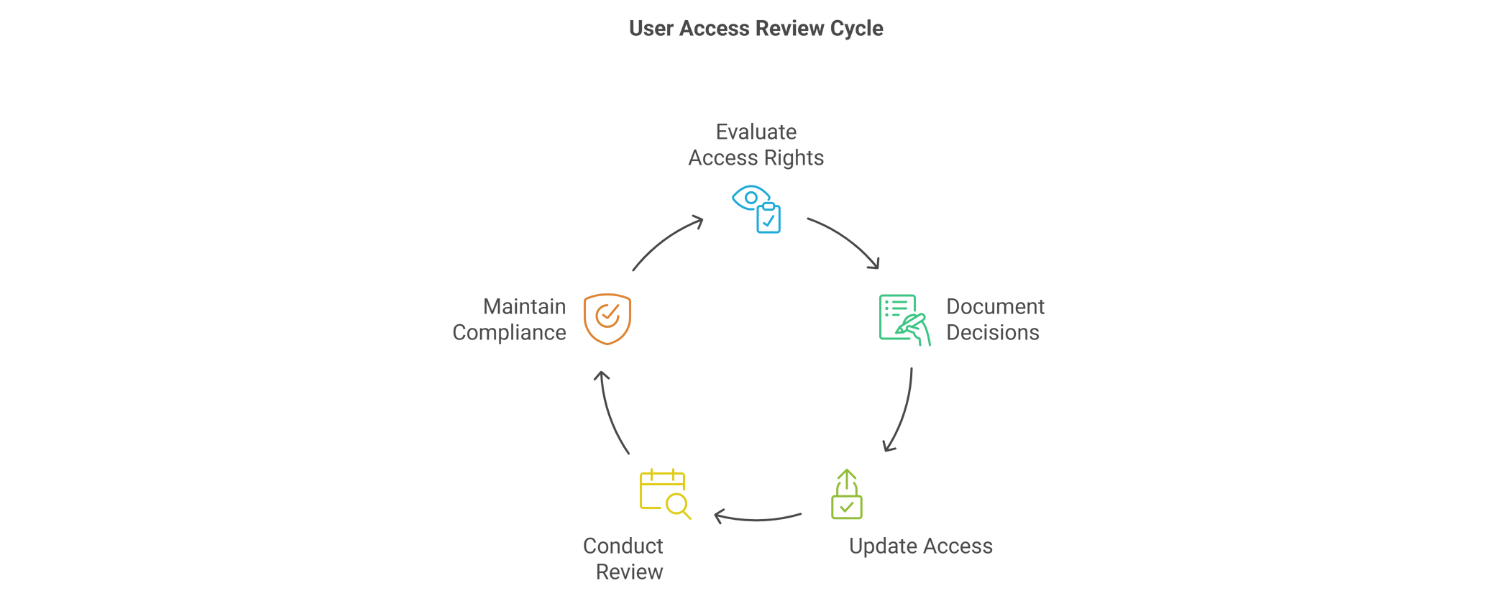
A User Access Review Template helps organizations standardize and simplify the process of reviewing user permissions across systems. Instead of manually collecting access data from multiple applications, a structured template provides a clear and repeatable format for documenting users, roles, access levels, and review decisions. This improves consistency, reduces human error, and significantly speeds up compliance audits and access certification cycles.
User access reviews are a critical component of identity governance and security programs. If you want to understand the broader framework, compliance requirements, and best practices behind these reviews, explore our comprehensive guide on User Access Review.
This blog focuses specifically on the User Access Review Template itself — what it includes, how to structure it, and how organizations can use it effectively to streamline their access review process.
2. What Is a User Access Review Template?
A User Access Review Template is a structured document designed to simplify and standardize the process of auditing user access across systems, applications, and data repositories. It typically functions as a checklist or spreadsheet that helps reviewers—such as IT administrators, department managers, or compliance officers—evaluate whether each user’s access rights are appropriate for their current role and responsibilities.
Within the broader framework of Identity and Access Management (IAM) and Identity Governance and Administration (IGA), an access certification template provides a consistent way to document access decisions, record review justifications, and identify potential access risks. Whether an employee has changed roles, transferred departments, or left the organization, the template ensures access permissions are regularly reviewed and updated.
Beyond compliance requirements, a User Access Review Template also improves operational efficiency by creating a centralized view of access information. Critical details such as user identity, assigned roles, application access levels, and review decisions can be tracked in a single document. This structured approach simplifies audit preparation and provides clear visibility into access governance activities.
For example, many organizations conduct quarterly or annual access certification campaigns using a customizable template. During these reviews, system owners or managers receive a list of users with their current access privileges and must verify whether that access should be approved, modified, or revoked. This structured workflow reduces manual errors and helps organizations maintain alignment with IAM policies, internal security controls, and regulatory requirements.
Now that we understand the purpose of a Access Review Template, the next section explores the key components that make an effective template for managing access reviews.
3. Key Components of a Robust User Access Review Template
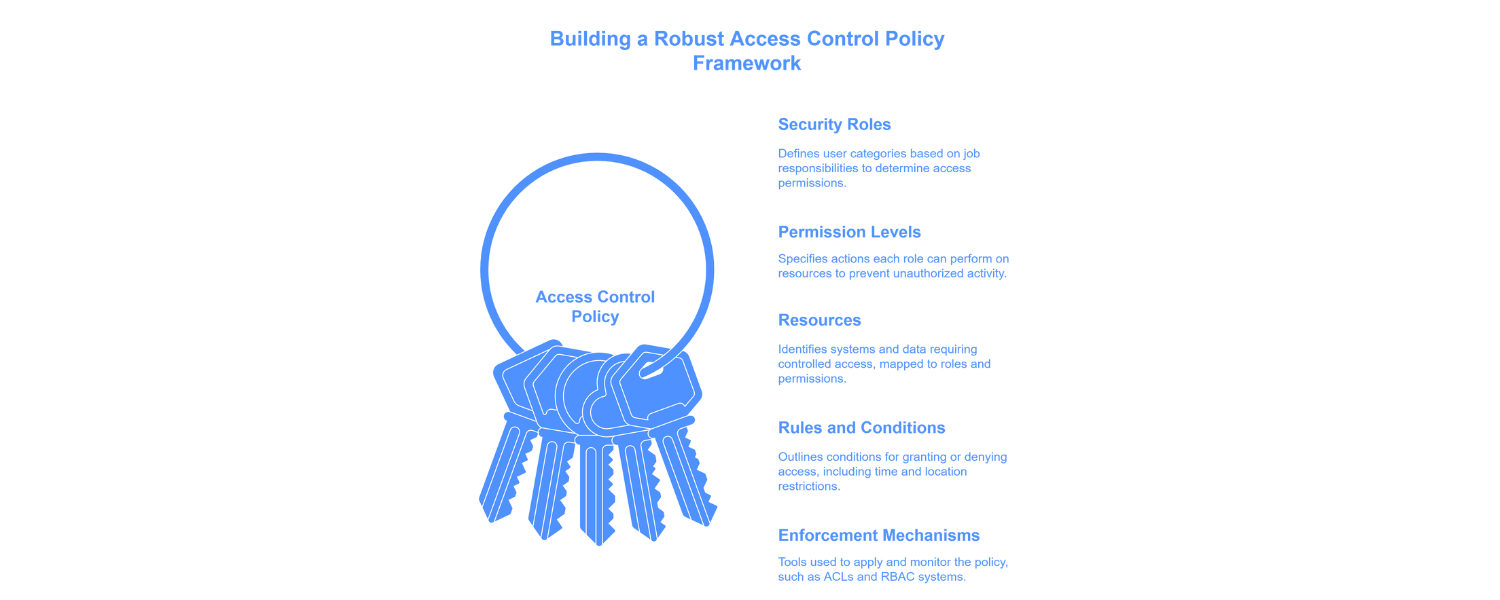
A well-structured User Access Review (UAR) template isn’t just a table of fields—it’s a strategic tool that helps organizations enforce least-privilege access, prevent internal threats, and ensure compliance with regulatory frameworks. By capturing specific, relevant data points, this template strengthens your organization’s Identity Governance and Administration (IGA) strategy and streamlines the review process for both IT and business stakeholders.
Whether you’re managing access manually or integrating with IAM platforms, the following components are essential to designing a review system that is clear, accountable, and audit-ready.
User Identification
To assess access rights effectively, reviewers must first understand who the user is, what their role entails, and where they fit within the organization. This section lays the foundation for Role-Based Access Control (RBAC).
Key Fields:
- Full Name
- Employee ID
- Department
- Job Title
- Manager/Supervisor
- Employment Status (Active/Inactive)
By centralizing this identity data, organizations can quickly spot mismatches between job roles and assigned permissions—a common issue flagged during internal IAM risk management audits.
Application & System Access Inventory
This section provides a granular view of every application or system the user can access. It’s especially useful when evaluating customer identity and access management setups or hybrid environments.
Key Fields:
- Application Name
- System Type (SaaS, On-Premise, Cloud, etc.)
- Access Level (Admin, Read-only, Editor)
- License Type
- Access Start Date
This information helps identify high-risk access, redundant permissions, or unused licenses—insights that support more efficient provisioning and help reduce attack surfaces.
Role & Permission Mapping
Mapping permissions to job responsibilities is critical in aligning with your identity governance and administration solutions. This section ensures that access rights are not only appropriate, but also justifiable.
Key Fields:
- Assigned Role – The functional role within the system (e.g., Finance Analyst, HR Admin).
- Privileges Granted – Specific actions permitted (e.g., Manage Users, Export Data).
- Role Justification – Explains why access is necessary, supporting access rationale.
- Does Role Match Job Function? – A yes/no validation to flag potential mismatches.
Regularly reviewing these fields prevents privilege creep and supports compliance with frameworks like ISO 27001 and SOX, which mandate role-based access reviews.
Reviewer Information
To maintain transparency and accountability, it’s important to document who is conducting the review and their relationship to the user.
Key Fields:
- Reviewer Name
- Reviewer Email
- Department
- Reviewer Role
- Date of Review
This data also supports traceability in audit logs and aligns with access certification processes tied to identity access management certifications.
Review Schedule
Access reviews should follow a consistent cadence based on user risk profiles, data sensitivity, and compliance requirements. This section makes it easier to manage those cycles.
Key Fields:
- Review Frequency – Typically set as Quarterly, Semi-Annual, or Annual.
- Last Reviewed Date – Helps track historical activity.
- Next Review Due Date – Allows planning and reminders for the next cycle.
- Reminder Status – Indicates if alerts were sent, pending, or escalated.
A reliable schedule enhances operational consistency and is key to maintaining strong IGA security practices.
Review Decision & Status
Documenting outcomes of each review is essential for action tracking and audit trails. This section captures final decisions, next steps, and any necessary justifications.
Key Fields:
- Decision (Approve / Modify / Revoke)
- Reason for Decision
- Pending Actions
- Follow-Up Required?
These fields help teams take swift, traceable action and can be integrated with platforms using SCIM API for real-time updates across systems.
Audit Trail & Comments
The final section supports compliance, internal governance, and historical reference. It creates a digital paper trail of what decisions were made, why, and by whom.
Key Fields:
- Reviewer Comments – Justifications, observations, or concerns logged during the review.
- Action Taken By – Who performed the action, along with their role.
- Timestamp of Change – Time and date of updates for audit records.
- Document Upload – Optional field for supporting evidence or approvals.
- Compliance Notes – Any notes related to regulations like GDPR, HIPAA, or SOX.
This layer of documentation is vital when aligning with Federated Identity & Access Management systems or preparing for third-party audits.
Together, these components form the backbone of an effective access review template. Up next, we’ll share a free downloadable template that includes all of these fields—ready for customization and deployment within your organization.
4. Download the Free User Access Review Template
After understanding the essential components of an effective User Access Review (UAR) template, the next step is implementation. To help your organization streamline the review process, we’ve created a ready-to-use access review template designed to support both IT and compliance teams. This template brings structure and consistency to access evaluations and can be easily adapted to fit into existing Identity Governance and Administration (IGA) workflows.
What’s Included in the Download?
The template is available in two formats—Excel and Google Sheets—and includes all the fields discussed in the previous section. Whether you’re conducting a quarterly review for privileged users or an annual audit of all employees, this template ensures every decision is documented, traceable, and compliant.
We offer two versions:
- Basic Version
- Pre-filled columns for quick access reviews
- Ideal for small teams or organizations starting with manual processes
- Printable for offline use or team sign-offs
- Advanced Version
- Includes conditional formatting to flag outdated or inactive access
- Drop-down menus for standardized review decisions
- Formula-based reminders for pending actions and due dates
- Integration-ready design that complements SCIM API configurations and lightweight IAM tools
- Includes conditional formatting to flag outdated or inactive access
These features help lay the groundwork for IGA security best practices while ensuring your reviews are consistent and audit-ready.
Customize It for Your Organization
No two organizations have the same access policies, applications, or compliance requirements. That’s why the template is fully editable. You can:
- Add or remove fields based on your access control policy
- Incorporate department-specific roles or job functions
- Align fields with external regulatory standards such as SOX, HIPAA, or ISO 27001
- Tag high-risk roles for additional scrutiny, in line with your IAM risk management strategy
Security teams can also link this template with their broader customer identity and access management process, especially when dealing with third-party access or federated environments.
Get the Template
Download your preferred version and start building a disciplined, compliant approach to access control:
[Download Basic Template (Excel)]
In the next section, we’ll cover the best practices for using this template effectively to ensure high review completion rates, improved accountability, and streamlined compliance audits.
5. Best Practices for Using the Template Effectively
To support robust Identity Governance and Administration (IGA) and reduce risk across the board, organizations should follow these best practices when using the template.
Schedule Regular Review Cycles
Consistency is key. Establish a formal cadence for access reviews—quarterly for high-risk departments like finance or IT, and semi-annually or annually for others. Frequent reviews help identify outdated access privileges early and mitigate threats before they escalate.
Tip: Use the “Review Schedule” fields in the template to automate reminders and track compliance over time.
Prioritize Critical Systems and Sensitive Data
Not all systems carry the same level of risk. Focus your attention on applications housing PII, financial data, or intellectual property. Align these with your IAM risk management strategy and ensure they’re covered in each cycle.
Example: Involve both IT and department heads when reviewing access to customer relationship management (CRM) tools, HR systems, or financial platforms.
Involve Multiple Stakeholders
While IT teams handle the technical side of Identity Access Management (IAM), line managers understand the functional roles of their team members. Involve both groups in the review process to ensure accurate access decisions. This collaborative approach reinforces Role-Based Access Control (RBAC) and validates that access privileges align with actual job functions.
Insight: Use the “Reviewer Information” and “Role Justification” sections in the template to encourage role-based evaluations.
Make Justification and Comments Mandatory
Every change—especially a revoke or modify action—should be backed by a valid reason. Mandating comments ensures transparency and accountability while strengthening internal controls. It also supports compliance frameworks like SOX and ISO 27001, which emphasize auditability and proper documentation.
Compliance Bonus: This aligns well with identity governance and administration solutions that require comprehensive access logs and reviewer accountability.
For guidance on implementing these templates effectively at scale, see our User Access Review Best Practices guide.
Archive Each Review Cycle
Store completed reviews securely for future audits and internal reference. This builds a reliable audit trail, simplifies governance reporting, and supports IGA security objectives. It also facilitates retrospective analysis, helping organizations understand how access patterns evolve over time.
Future-Proofing: This archival process can be easily migrated to automated Federated Identity & Access Management platforms when you’re ready to scale.
By incorporating these best practices, your access reviews become more than a compliance checkbox—they evolve into a proactive layer of defense against insider threats and data breaches. In the next section, we’ll show you how to align this review process with global compliance standards like GDPR, HIPAA, and SOX to ensure full regulatory coverage.
6. Aligning Your Template with Compliance Standards
A well-designed Access Review Template plays a pivotal role in fulfilling the access control, auditability, and documentation requirements set forth by industry regulations such as GDPR, HIPAA, SOX, and ISO 27001.
By incorporating structured reviews, centralized tracking, and documented reviewer decisions, the template aligns seamlessly with both security and compliance goals—particularly in the broader context of Identity Governance and Administration (IGA) and Identity Access Management (IAM) frameworks.
How the Template Supports Key Compliance Standards
| Regulation | Compliance Requirement | How the Template Helps |
| GDPR | Enforces data access minimization and control over personal data | Fields like “Access Level,” “Job Role,” and “Role Justification” ensure only necessary access is granted and reviewed regularly |
| HIPAA | Requires regular audits of user access to protected health information (PHI) | “Review Schedule,” “Reviewer Comments,” and “Audit Trail” support access transparency and documentation |
| SOX | Demands controls over financial system access and audit trails | “Access Start Date,” “Decision Status,” and “Reviewer Info” create accountability and visibility for financial access points |
| ISO 27001 | Calls for documented access policies, user reviews, and corrective actions | Template enables periodic reviews and provides clear evidence of user access controls and compliance tracking |
This mapping ensures that the review process is not only operationally efficient but also defensible during audits.
Extending Compliance with IGA & IAM Tools
When integrated with broader IGA solutions or IAM risk management systems, the review process becomes even more powerful. For instance:
- Pairing the template with a Federated Identity & Access Management tool can streamline access tracking across multiple platforms
- Incorporating SCIM API standards enables automated provisioning and deprovisioning, keeping your access lists always up to date
- Using identity-focused tools also helps meet identity governance and administration solutions requirements with minimal manual overhead
Bonus: Many organizations seeking identity access management certifications can use this template and its outputs as supporting documentation during audit preparation or tool evaluations.
When properly implemented and maintained, an access review template becomes more than an operational tool—it becomes a strategic asset for maintaining compliance and strengthening an organization’s security posture.
In the next section, we’ll explore when and why it makes sense to transition from manual templates to automated user access review tools, especially as organizations grow in size and complexity.
7. When to Move from Manual Template to Automated Tools
While a well-structured User Access Review Template is a powerful starting point, growing organizations eventually face limitations with manual processes. As user counts rise, systems multiply, and compliance requirements intensify, manual reviews become harder to manage, more error-prone, and less scalable.
This is where automation steps in—not to replace your efforts, but to enhance them.
Signs It’s Time to Scale Beyond Spreadsheets
If any of the following apply to your organization, it may be time to shift to automated IGA solutions or IAM risk management tools:
- Your workforce includes hundreds or thousands of users, including third-party vendors and contractors
- Role changes, project transitions, or department shifts happen frequently
- You’re preparing for or recovering from compliance audits and need ongoing access traceability
- Manual coordination between departments delays review cycles or leads to inconsistent documentation
These are clear indicators that your organization needs an access management solution with more automation, accuracy, and control.
Benefits of Moving to IAM and UAR Tools
Upgrading to automated Identity and Access Management (IAM) platforms or user access review tools provides several benefits that significantly enhance the efficiency, scalability, and accuracy of access reviews.
- Real-time Access Monitoring
Track and log access events instantly across systems, enabling continuous review instead of periodic check-ins.
- Auto-Remediation Capabilities
Revoke or modify access automatically when violations or mismatches are detected—without waiting for the next review cycle.
- Role-Based Access Control (RBAC) Enforcement
Align access permissions to job functions dynamically, minimizing privilege creep and strengthening IGA security.
- Built-in Reporting & Audit Trails
Generate exportable audit logs, reviewer notes, and compliance evidence without manually assembling documentation.
- Federated Identity & Access Management
Unify access management across cloud and on-prem environments, enabling central oversight even in hybrid IT ecosystems.
- SCIM API Integration
Seamlessly connect identity systems, HR databases, and apps to ensure that user access reflects real-time changes in employment status or job function.
By adopting these tools, businesses gain agility, reduce human error, and better align with identity governance and administration solutions best practices.
Pro Tip: For organizations pursuing Best practices for identity access management certifications, automated UAR platforms offer built-in features that satisfy most audit readiness requirements—saving time, effort, and stress.
Although the transition from manual to automated may seem daunting, the long-term advantages far outweigh the short-term learning curve. And if your team has already adopted a structured review template, you’re halfway there.
8. Conclusion
As organizations manage an increasing number of systems, applications, and user accounts, maintaining clear visibility over who has access to what becomes essential. Without a structured process, access reviews can quickly become inconsistent, time-consuming, and difficult to audit. This is where a well-structured User Access Review Template becomes invaluable.
A standardized template provides a simple and repeatable framework for documenting users, roles, system permissions, and review decisions. By centralizing this information in one place, organizations can conduct access reviews more efficiently, reduce the risk of excessive permissions, and maintain clear documentation for security audits and compliance requirements.
Beyond simplifying the review process, using a structured template also supports broader identity security initiatives such as Identity Governance and Administration (IGA), Identity and Access Management (IAM), and Role-Based Access Control (RBAC). With consistent documentation and review workflows, organizations can better enforce least-privilege access and maintain stronger control over sensitive systems and data.
While many organizations eventually adopt automated user access review tools as their environments scale, a well-designed template is often the first step toward building a mature and reliable access governance process. It helps teams establish clear review practices that can later integrate seamlessly with more advanced IAM and IGA solutions.
9. FAQs
1. What is an access review template?
An access review template is a structured document used to evaluate and document user permissions across systems, applications, and data resources. It typically includes fields such as user identity, job role, system access, permission level, reviewer decision, and justification. Using a standardized format helps organizations conduct consistent access audits and maintain proper documentation for security and compliance purposes.
2. How do you use an access review template?
Organizations usually begin by exporting user access data from applications, directories, or identity platforms. This information is then recorded in the template, where managers or system owners review each user’s permissions and decide whether to approve, modify, or revoke access. Documenting these decisions helps create a clear audit trail for compliance and future review cycles.
3. What information should an access certification template include?
A well-designed access certification template typically includes the following fields:
User ID or employee name
Department or job role
System or application name
Access level or permission type
Reviewer name
Review decision (approve, revoke, modify)
Comments or justification
Review date
Capturing these details ensures the review process remains transparent, repeatable, and audit-ready.
4. How often should organizations conduct access reviews?
The frequency of access reviews depends on internal security policies and regulatory requirements. Many organizations review access to critical systems on a quarterly basis, while lower-risk applications may be reviewed annually or semi-annually. Maintaining a consistent review schedule helps enforce least-privilege access and supports compliance with frameworks such as SOX, HIPAA, GDPR, and ISO 27001.
5. When should organizations move from manual templates to automated tools?
Manual review templates work well for smaller organizations or teams beginning their access governance programs. However, as the number of users, systems, and permissions grows, manual processes can become difficult to manage. At this stage, organizations often adopt IAM platforms or access review tools to automate certification cycles, send notifications, and generate real-time compliance reports.
6. Is there a free access review template available?
Yes. Many organizations start with a free access review template to standardize how permissions are evaluated across systems and applications. These downloadable templates typically include fields for user information, system access, permission levels, reviewer decisions, and comments. Using a ready-made format helps teams quickly implement a structured review process without creating one from scratch.
7. What format works best for an access review template?
Access review templates are most commonly created in Excel or spreadsheet format because they allow teams to easily document users, roles, permissions, and review outcomes. Spreadsheets also make it easy to filter users by department, application, or access level during review cycles. As organizations scale, these templates can later be integrated into IAM or identity governance platforms to automate access certification workflows.


