Credential Entitlement Management
Automate user access reviews to accelerate access certifications.
Stop the manual spreadsheet madness! Maintain compliance, prevent unauthorized access, and proactively monitor and audit access across your enterprise, cloud, and custom applications with SecurEnds.
Credential Entitlement Management (CEM) in 4 Easy Steps
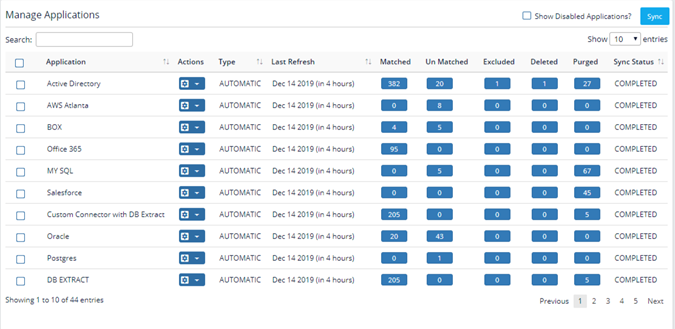
Step 1: Connect Applications
Manage identities from connected and disconnected applications across the IT landscape. CEM matches identities to the system of record using CSV uploads, pre-built connectors, flex connectors, or Service Desk integration. CEM integrates with your ITSM system (eg., ServiceNow, JIRA) to update the changes.

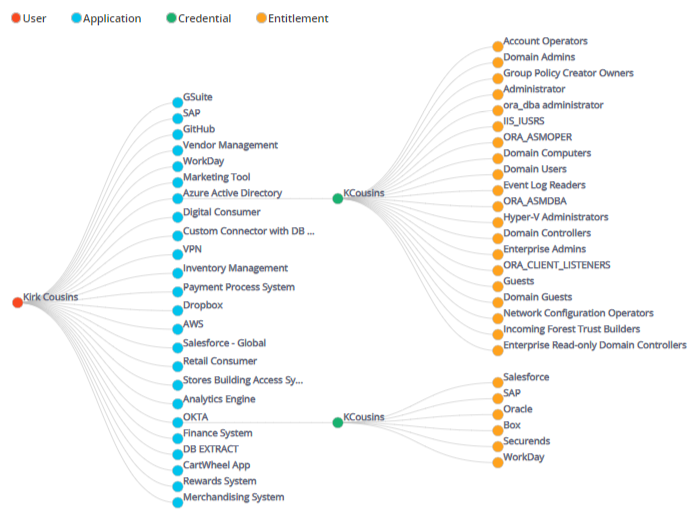
Step 2: Discover Identities
Centralize access controls and consolidate identity repositories. Powered by artificial intelligence and machine learning, Discovery Module enables auto-discovery of identities, including orphaned and unauthorized accounts.
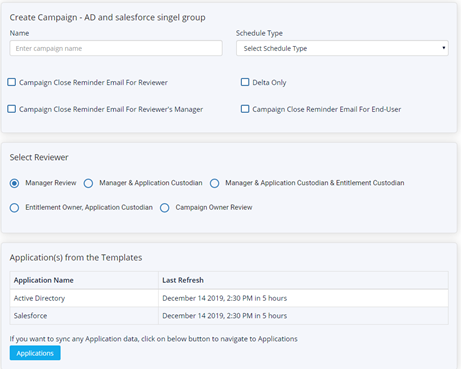
Step 3: Intelligent Campaigns
Schedule automated access review campaigns by multiple dimensions (e.g., role). Utilize intelligent reminders to drive action from end-users, approvers, and skip level approvers. View changes since the last review through “Delta Campaign” functionality.
Step 4: Reports & Insights
Our reports module presents a simplified analytics workflow for outliers based on their risk profiles and excessive privileges. Drill down by campaigns, applications, and periods.
CEM
Delivers >
30 Days
A Fortune 500 with 4700 employees was able to achieve its audit target across 100+ on-prem and cloud applications in 30 days.
Customer Success Story
Challenge
Each year SITA’s Internal Audit department reviews multiple applications worldwide in accordance with ISO27001 standards and their internal controls. A large focus of this review is validating User Access Control, including credentials and entitlements. Auditors undertake a manual process to review 4700 employees with their managers and then work with Security Teams and Help Desks to modify access. The process is then required to be repeated every three months.
Testimonial
The CEM solution from SecurEnds has provided our company with a solution that enables us to pass internal and external audits for access control. We don’t have to use spreadsheets, emails and many hours of manual review to complete our credential and entitlement reviews. Plus, we reduce our risk exposure by deleting unused accounts every quarter.
Steve Mosley – Security & Compliance, SITA.
Learn how SecurEnds CEM works.
Fill out the form below to get started.


