Advanced Threat Detection for APIs & Applications
Advanced Threat Detection for APIs & Applications
Detect, analyze, and stop real time API threats, abuse, and anomalies before they impact your business. Stay ahead of attacks with AI powered intelligence and proactive protection.

Modern Threats Bypass Traditional Security Controls
Signature based systems fail to detect anomalies. Static rules cannot handle dynamic or contextual threats, leaving APIs vulnerable.
APIs Bypassing WAFs
Modern APIs often bypass traditional WAFs, leaving endpoints exposed. This blind spot increases the risk of unauthorized access and attacks.
Bot Driven API Abuse
Automated scripts and bots exploit API endpoints for scraping and fraud. API threat detection is required to identify and stop these attacks in real time.
Token Misuse & Credential Stuffing
Stolen tokens allow attackers to bypass authentication. Credential stuffing can compromise accounts, causing revenue and data loss.
Business Logic Attacks
Attackers exploit flaws in workflow and logic, bypassing conventional security controls. Real time monitoring catches these sophisticated attacks before they escalate.
Unknown Attack Patterns
Zero day and emerging threats evade signature based detection. Advanced threat detection and behavioral monitoring are crucial to protect APIs and applications.
What is Threat Detection in API Security?
Threat detection continuously monitors API traffic to identify malicious activity. It analyzes requests in real time, detects abnormal patterns, and alerts teams before attacks impact applications. By combining behavioral analysis and AI driven insights, it ensures fast and actionable protection.
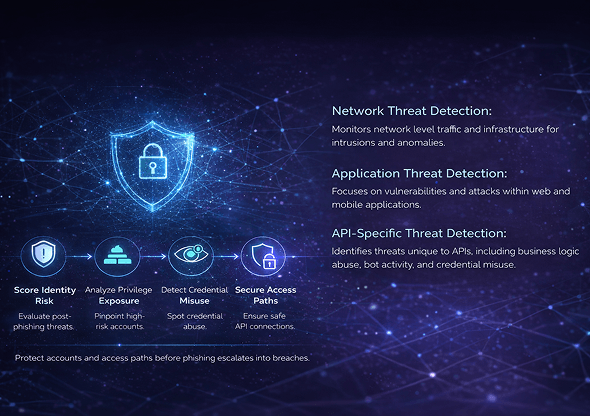
Network Threat Detection:
Monitors network level traffic and infrastructure for intrusions and anomalies.
Application Threat Detection:
Focuses on vulnerabilities and attacks within web and mobile applications.
API-Specific Threat Detection:
Identifies threats unique to APIs, including business logic abuse, bot activity, and credential misuse.
Comprehensive Threat Detection Coverage
API Abuse & Business Logic Attacks
Detects data scraping, inventory hoarding, rate manipulation, and workflow abuse. Behavioral monitoring identifies patterns that signature based tools miss. Protect your APIs from misuse that can lead to revenue loss and operational disruption.
Injection Attacks
Identify SQL, command, and JSON injections targeting APIs and applications. Prevent unauthorized access and data corruption before it spreads. Application threat detection ensures endpoint integrity across services.
Authentication & Authorization Attacks
Block token replay, Broken Object Level Authorization, and privilege escalation. Real time scoring prioritizes high risk events to reduce response time. AI-powered threat detection strengthens access controls and prevents account compromise.
Bot & Automated Threats
Mitigate credential stuffing, account takeover, and fake account creation. Behavioral threat detection flags suspicious automation patterns. Protect sensitive data and prevent fraudulent transactions efficiently.
Zero Day & Unknown Threats
Detect unknown attacks using anomaly detection and AI-driven threat intelligence. Consistent learning adapts to new attack vectors without signature updates. Ensure proactive API attack detection for emerging threats.
How Our Real Time Threat Detection Works

Traffic Monitoring
We inspect every API call in depth, analyzing headers and parameters. Consistent monitoring captures suspicious activity across all endpoints. This ensures API threat detection identifies possible attacks immediately.

Behavioral Baseline Creation
Our engine learns normal API behavior over time to spot deviations. Abnormal usage patterns are flagged in real time for review. This behavioral threat detection prevents unnoticed abuse and anomalies.

AI & Risk Based Scoring
Dynamic threat scores are assigned to every detected anomaly. Critical threats are prioritized to ensure rapid incident response. AI powered threat detection reduces false positives while focusing on real risks.

Automated Response
Malicious IPs can be blocked, rate limiting applied, and tokens revoked automatically. SOC teams receive immediate alerts for fast mitigation. This enables real time threat detection and response without disrupting legitimate traffic.
Advanced Threat Detection Capabilities
Real Time API Threat Detection
Consistent monitoring identifies attacks the moment they occur. Prevent breaches and secure sensitive data proactively.
Behavioral Anomaly Detection
Detects unusual activity across endpoints and traffic flows. Behavioral analysis uncovers threats signature based tools miss.
AI-Powered Risk Scoring
Assign threat scores dynamically based on context and history. Focus remediation on the highest-risk events first.
OWASP API Top 10 Protection
Automatically enforce safeguards against the most common API vulnerabilities. Protect critical business and customer data.
Bot Detection & Mitigation
Identify automated attacks and malicious scripts targeting APIs. Prevent account takeovers and credential abuse.
Sensitive Data Exposure Alerts
Detect and alert on exposure of PII, financial, and confidential data. Reduce compliance and breach risks across cloud and on-prem environments.
Context Aware Policy Enforcement
Apply security policies intelligently based on API context. Reduce unnecessary blocks and ensure seamless user experience.
Consistent Attack Surface Monitoring
Monitor all APIs across environments for new and emerging threats. Ensure complete visibility into your cloud threat detection posture.
Unified Threat Detection Across Your Ecosystem
Multi-Cloud Environments
Our API threat detection works smoothly across AWS, Azure, and GCP, giving full visibility into all cloud workloads. Monitor traffic and anomalies in real time without impacting performance. Ensure consistent security and compliance across multi-cloud deployments.
API Gateways
Integrates with API gateways to track all exposed endpoints and traffic flows. Detect malicious requests, abuse, or misconfigurations instantly. This real time threat detection strengthens your gateway security posture
Kubernetes & Microservices
Protect containerized applications and microservices with consistent monitoring. Behavioral analysis identifies unusual API calls and inter service anomalies. Supports secure deployments in dynamic, containerized environments.
Hybrid Infrastructure
Monitor APIs across on-premises and cloud environments in a unified way. Advanced threat detection ensures consistent protection across hybrid architectures. Reduce blind spots and enforce security policies everywhere.
Edge Deployments
Secure APIs deployed at the edge, including IoT and CDN endpoints. Real time monitoring detects abuse closer to the source of traffic. Maintain compliance and performance without sacrificing security.
Why Partner with Us as Your API Security Company?
Reduced Breach Risk
Consistent API threat detection identifies malicious activity early, minimizing the chance of breaches. Protect your critical applications and sensitive data from evolving attacks.
Faster Incident Response
Real time alerts and automated actions enable teams to respond immediately to threats. Threat detection and response reduces downtime and mitigates potential damage.
Lower False Positives
AI-driven behavioral monitoring distinguishes real threats from harmless anomalies. This ensures SOC teams focus on critical issues without unnecessary alerts.
Protection of Sensitive Data
Detects exposure of PII, financial, and confidential information across APIs. Application threat detection safeguards sensitive data from unauthorized access.
Compliance Readiness
Monitor and report on all API activity to meet standards like PCI, HIPAA, and GDPR. Maintain audit ready logs with real time threat detection capabilities.
Reduced Revenue Loss from API Abuse
Prevent account takeover, bot attacks, and scraping which can impact revenue. Advanced threat detection ensures business continuity and customer trust.
Threat Detection Use Cases
Facebook API Account Exposure
In 2019, a vulnerability in Facebook’s API exposed personal data of 540 million users after attackers accessed overly permissive tokens. This incident highlighted how weak API authentication can lead to massive breaches. It underscored the need for real time API threat detection to prevent unauthorized access.
LinkedIn Data Scraping Incident
In 2021, LinkedIn suffered an API data scraping issue that exposed information for 700 million profiles. Attackers harvested user data due to lax API access controls. This shows why API attack detection and behavior analysis are essential to stop abuse.
T‑Mobile API Exploit
In 2020, attackers exploited a T‑Mobile API to access personal information for over 40 million customers. The breach occurred through an unsecured endpoint lacking proper authentication. This real breach highlights why application threat detection must go beyond perimeter defenses.
What Makes Our Threat Detection Different
AI-Driven Behavioral Detection
Detects threats beyond signatures using AI and behavioral analysis. Behavioral threat detection uncovers anomalies hidden from traditional tools.
API Specific Threat Intelligence
Tailored detection models understand API traffic patterns and business logic. API threat detection becomes precise, reducing false positives.
Zero Code Deployment
Integrate in minutes with no application changes. Start protecting APIs immediately without development delays.
Low False Positives
Advanced scoring prioritizes critical alerts and reduces noise. SOC teams focus on high-risk incidents for faster resolution.
Contextual Risk Prioritization
Threats are scored based on sensitivity, traffic behavior, and impact. Focus remediation where it matters most.
Consistent Learning Engine
Adapts to new API threats automatically. Ensure real time threat detection keeps pace with evolving attack methods.

Deploy Threat Detection Without Disrupting Development
Agentless Deployment
Our platform deploys without installing agents, so it doesn’t interfere with existing infrastructure. Teams can start monitoring APIs and applications immediately, ensuring full visibility from day one.
API Gateway Integration
It integrates smoothly with API gateways to track all traffic and detect anomalies in real time. It allows real time API threat detection without affecting performance.
CI/CD Integration
Our solution connects directly with CI/CD pipelines to scan APIs before they are deployed. This ensures vulnerabilities are identified early, reducing the risk of insecure releases.
DevSecOps Compatibility
Threat detection fits naturally into DevSecOps workflows, enforcing security during development. Advanced threat detection protects APIs while supporting agile software delivery.
SOC Integration
Alerts and insights feed directly into Security Operations Centers for rapid response. Teams can act quickly on high risk threats, enabling efficient threat detection and response.
Audit Ready Threat Detection & Reporting
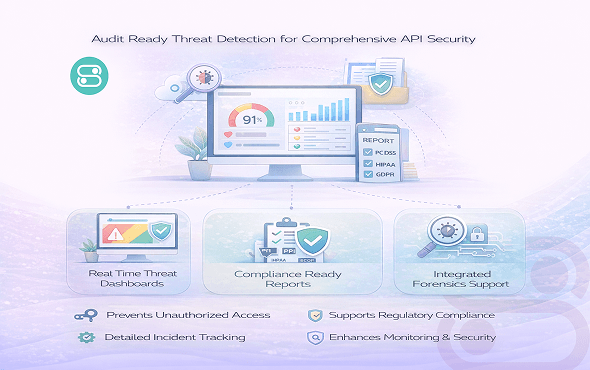
Our platform provides audit ready threat detection which ensures security and compliance across all APIs and applications. Real time dashboards give teams a clear view of threats as they emerge. Extensive reports meet regulatory requirements like PCI, HIPAA, and GDPR. Incident history tracking allows for detailed post attack analysis, and integrated forensics support helps investigate and remediate breaches efficiently.
- Real time threat dashboards for instant visibility
- Compliance ready reports for audits and regulations
- Detailed incident history tracking for post event analysis
- Integrated forensics support to investigate and remediate incidents
Frequently Asked Questions
Threat detection is the monitoring of APIs and applications to identify malicious activity and suspicious behavior before it can cause harm.
API threat detection analyzes incoming and outgoing traffic. It identifies anomalies in requests and alerts security teams to stop possible attacks.
Behavioral threat detection identifies unusual patterns of activity, comparing them to normal behavior to catch threats which signature based systems might miss.
A WAF relies on static rules and signatures, whereas threat detection monitors behavior and context to detect attacks in real time.
AI improves threat detection by scoring risks dynamically, finding unknown attack patterns, and reducing false positives for faster and smarter responses.
Protect Your APIs & Applications Today
Detect, prevent, and respond to API threats before they impact your business. Gain full visibility and actionable insights with AI powered threat detection.


